Unlock a world of possibilities! Login now and discover the exclusive benefits awaiting you.
- Qlik Community
- :
- Blogs
- :
- Technical
- :
- Design
- :
- Why security rules in Qlik Sense?
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
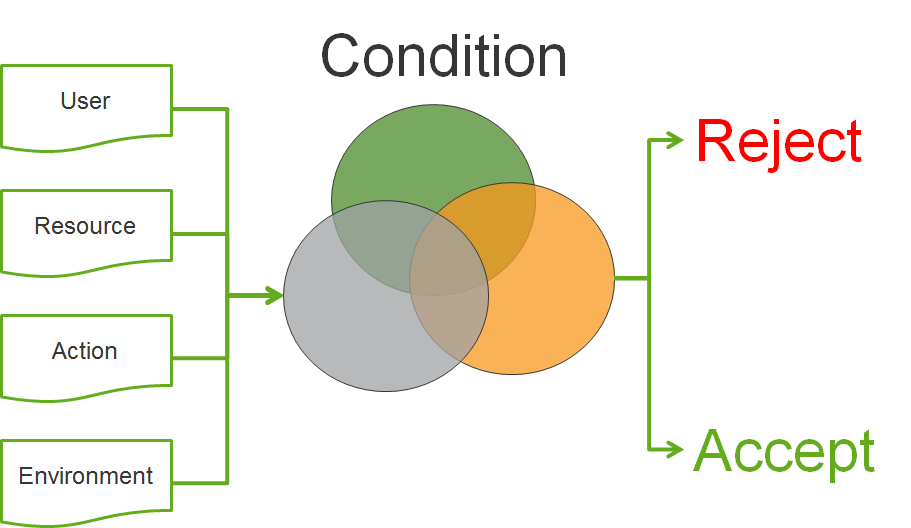
Qlik Sense uses Attribute Based Access Control (ABAC) as a basis for its security. In this post I will explain why we decided to implement this, and give you an understanding of the future of access control.
Is it only Qlik that thinks that ABAC is the future of access control? No
When Gartner predicts the future of access control, they say
“By 2020, the majority of enterprises will use attribute-based access control (ABAC) as the dominant mechanism to protect critical assets, up from less than five percent today.” (http://www.issa.org/resource/resmgr/JournalPDFs/feature0614.pdf)
And the National Institute of Standard and Technology (NIST) has released a special publication to raise awareness and help with making effective implementations of ABAC (NIST SP 800-162 http://nvlpubs.nist.gov/nistpubs/specialpublications/NIST.sp.800-162.pdf)
If this is the future, what is then ABAC? I have taken the liberty of changing the NIST definition of ABAC to be consistent with the syntax (marked in bold green) that is used in Qlik Sense.
An access control method where user requests to perform actions on resources are granted or denied based on assigned attributes of the user, assigned attributes of the resource, environment conditions, and a set of security rules that are specified in terms of those attributes and conditions.
This sounds pretty generic. So why is ABAC seen as an important step into the future of access control?
The first major benefit is that with ABAC you can implement other well-known access control methods such as mandatory access control (MAC), identity based access control (IBAC) and role-based access control (RBAC). This makes it very flexible and therefore suitable to solve most company’s security needs.
But are there other benefits? Yes.
You can develop an access control policy independent of users
We have a language that can be used to describe security policies that Qlik Sense understands and be used to enforce the security controls needed.
Accommodating the unanticipated/external user
We can describe the security controls using attributes of resources and users. With this approach new users accessing the system will be in compliance with defined policies, and access will be granted based on the assigned attributes. No additional configuration is needed in Qlik Sense.
Avoid role/group explosion
Using logic conditions in our rules, we no longer need to create new roles/groups to grant new subsets of user access.
Easier management
The administrators of the system don't need to understand or change the security policy; they only have to ensure that resources and users are correctly described by their attributes for them to be in compliance with the security policy.
Cater for taking more things into consideration for security decisions such as dynamic attributes (environment)
With ABAC we can start using the environment (the context in which the security decision is made, e.g. if the connection to the system is encrypted or not) to describe our security policy.
Hopefully this has provided you insights to why ABAC is the future of access control and the benefits this will bring to your Qlik Sense deployments. If you have questions on this blog post or have ideas of what you want to read in the future please don’t hesitate to comment this post.
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.