Unlock a world of possibilities! Login now and discover the exclusive benefits awaiting you.
- Qlik Community
- :
- Support
- :
- Support
- :
- Knowledge
- :
- Support Articles
- :
- CVE_2021_44228 - Handling the log4j lookups critic...
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
CVE_2021_44228 - Handling the log4j lookups critical vulnerability for Qlik Replicate
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
CVE_2021_44228 - Handling the log4j lookups critical vulnerability for Qlik Replicate
Jan 25, 2022 7:47:50 AM
Dec 13, 2021 3:25:57 PM
Qlik is providing these mitigation steps as a temporary measure. A patch will be provided and linked here; customers are advised to move to the patch as soon as it is available.
Patches are available. See Vulnerability Testing - Apache Log4j, reference CVE-2021-44228 (also referred to as Log4Shell) for your release and the relevant patch.
Upgrade at the earliest.
Environment:
Mitigation steps to follow Replicate log4j vulnerability:
Mitigation - Endpoint Server - Windows
- Edit the file <installation-root>\Replicate\endpoint_srv\bin\rependctl.bat
(<installation-root> typically refers to C:\Program Files\Attunity) - Add the string -Dlog4j2.formatMsgNoLookups=true in the highlighted location shown below (last line of script):
@echo off
REM attunity endpoints server configuration/run script
FOR %%A IN ("%~dp0..") DO SET AT_PROD=%%~fA
REM list plugins here
SET AT_PLUGIN_LIST=-plugins rependsrv
REM set data directory based on the name of this script
SET AT_DATA_SUFFIX=
FOR /F "tokens=2 delims=_" %%A IN ("%~n0") DO SET AT_DATA_SUFFIX=%%A
IF "%AT_DATA_SUFFIX%" == "" (
SET AT_DATA=
) ELSE (
SET AT_DATA=-d data_%AT_DATA_SUFFIX%
)
IF EXIST "%AT_PROD%\jvm" (
SET AT_JAVA=%AT_PROD%\jvm\bin\java.exe
) ELSE IF EXIST "%AT_PROD%\..\jvm" (
SET AT_JAVA=%AT_PROD%\..\jvm\bin\java.exe
) ELSE IF "%JAVA_HOME%" == "" (
ECHO ERROR: JAVA Cannot be found
EXIT /b -1
) ELSE (
SET AT_JAVA=%JAVA_HOME%\bin\java.exe
)
SET AT_EXTERNAL=%AT_PROD%\externals
SET AT_LIB=%AT_PROD%\lib
SET AT_MAIN=com.attunity.infrastructure.server.PluginServer
REM <--------------- Fix Here ------------→
"%AT_JAVA%" -XX:+UseG1GC -Dlog4j2.formatMsgNoLookups=true -Dfile.encoding=UTF-8 %AT_JVM_OPT% -cp "%AT_EXTERNAL%"/*;"%AT_LIB%"/* %AT_MAIN% %AT_DATA% %AT_PLUGIN_LIST% %* - Save the file.
- Locate the vulnerable log4j-core-<version#>.jar file and rename/move it to ..\log4j-core-<version#>.jar-vulnerable.
$ cd <installation-root>\Replicate\endpoint_srv\externals\ $ ren log4j-core-<version#>.jar ..\log4j-core-<version#>.jar-vulnerable - Download the non-vulnerable jar named
log4j-core-nolookup-<version#>.jarfrom this page and place it in the same location as the vulnerable jar. - Restart the Replicate Windows service with the command:
$ sc stop AttunityReplicateServer
$ sc start AttunityReplicateServer
Note that if you have customized Replicate start scripts or if you are running multiple instances of Replicate on the same machine, you will have to repeat this process for the different environments and perform the equivalent edit on your modified start scripts.
Mitigation - Endpoint Server - Linux
- Edit the file <installation-root>/replicate/endpoint_srv/bin/rependctl.sh (<installation-root> typically refers to /opt/attunity)
- Add the string -Dlog4j2.formatMsgNoLookups=true in the highlighted location shown below (last line of script):
#!/bin/bash
# attunity endpoints server configuration/run script
DIR="$( cd "$( dirname "${BASH_SOURCE[0]}" )" >/dev/null && pwd )"
AT_PROD="${DIR}/.."
AT_PLUGIN_LIST="rependsrv"
if [ -d "${AT_PROD}/jvm" ]; then
AT_JAVA="${AT_PROD}/jvm/bin/java"
elif [ -d "${AT_PROD}/../jvm" ]; then
AT_JAVA="${AT_PROD}/../jvm/bin/java"
elif [ -z "$JAVA_HOME" ]; then
echo "ERROR: JAVA Cannot be found"
exit -1
else
AT_JAVA="${JAVA_HOME}/bin/java"
fi
AT_EXTERNAL="${AT_PROD}/externals"
AT_LIB="${AT_PROD}/lib"
AT_MAIN="com.attunity.infrastructure.server.PluginServer"
if [ -z "$AT_DATA" ]; then
AT_DATA="${AT_PROD}/data"
fi
AT_CP="${AT_EXTERNAL}/*:${AT_LIB}/*"
# <----------- Fix Here --------->
"${AT_JAVA}" -XX:+UseG1GC -Dlog4j2.formatMsgNoLookups=true -Dfile.encoding=UTF-8 ${AT_JVM_OPT} -cp "${AT_CP}" "${AT_MAIN}" -d "${AT_DATA}" -plugins "${AT_PLUGIN_LIST}" "${@:1}" - Save the file.
- Locate the vulnerable log4j-core-<version#>.jar file and rename/move it to ..\log4j-core-<version#>.jar-vulnerable.
$ cd <installation-root>/replicate/endpoint_srv/externals $ mv log4j-core-<version#>.jar ../log4j-core-<version#>.jar-vulnerable - Download the non-vulnerable jar named
log4j-core-nolookup-<version#>.jarfrom this page and place it in the same location as the vulnerable jar. - Restart the Replicate service with the command:
# service areplicate restart
Note that if you have customized Replicate start scripts or if you are running multiple instances of Replicate on the same machine, you will have to repeat this process for the different environments and perform the equivalent edit on your modified start scripts.
Mitigation - Client Samples in Java
The client samples are intended for demonstration - if they were used to build an application, make sure the application uses the latest version of the log4j component (v2.15) or, alternatively, apply similar mitigation to the ones listed above by adding the system property.
For more information on the Log4j vulnerability, please visit the Support Updates Blog post.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
@RAFFYUY27 I have updated the zip to remove the unnecessary files.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
1) On step#5 above, don't I need to remove the 'nolookup' from the new jar file?
2) On the provided .zip file, there are also log4j-api and log4j-core 2.16.0. Can't we simply put those files on <installation-root>\Replicate\endpoint_srv\externals folder?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
We have tested using Log4j-core and api version 2.16 in a DEV server, apparently all worked fine, tested different logging levels, stop/start tasks and etc.
However, that's not what Qlik recommended above, so as I don't want to get into that supported or non-supported dilemma, I'll go with the procedure above, which by the way is missing one step: renaming the nonlookup word from the file. So from log4j-core-nolookup-2.11.1.jar to log4j-core-2.11.1.jar for example.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hello @RAFFYUY27 ,
There is explanation in Apache site: https://logging.apache.org/log4j/2.x/security.html
I'm paste the sentence here:
Note that only the log4j-core JAR file is impacted by this vulnerability. Applications using only the log4j-api JAR file without the log4j-core JAR file are not impacted by this vulnerability.Hope this helps.
Regards,
John.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi Qlik team please conform whether we need to rename the uncompressed zip file from log4j-core-nolookup-2.11.1.jar to log4j-core-2.11.1.jar ?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hello @km1003 ,
the necessary steps are:
1. download the zip file;
2. unzip the compress file;
3. copy a given version .jar from the uncompressed folder to the original location and rename it to the original name eg "log4j-core-2.11.1.jar".
Hope this helps.
Regards,
John.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Where is the jar file to download from this web page?
Hengjun
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
We did not find the link to download on this web page and instruction did not say the file name with version (zip file) to download. Do we download the most recent version or version 2.11.1 if it is from Appache web site?
https://logging.apache.org/log4j/2.x/security.html
Thanks
Hengjun
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
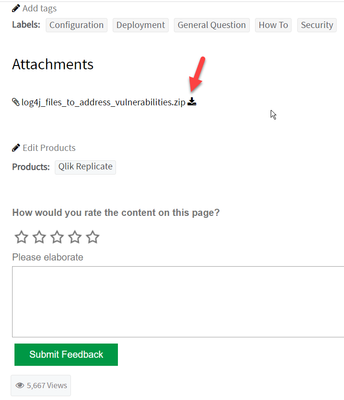
Hello HengJun, @liuhengjun ,
It's in this page , the bottom of the original article body, I marked it in red here:
Hope this helps.
Regards,
John.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi, John
Thanks for help. I did not notice the attachment earlier.
I downloaded and extracted log4j-core-nolookup-2.11.1.jar from the attachment link in this page. will apply remediation for Replicate 7.0.
Hengjun