Unlock a world of possibilities! Login now and discover the exclusive benefits awaiting you.
- Qlik Community
- :
- Support
- :
- Support
- :
- Knowledge
- :
- Support Articles
- :
- How to change the certificate used by the Qlik Sen...
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
How to change the certificate used by the Qlik Sense Proxy to a custom third party certificate
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How to change the certificate used by the Qlik Sense Proxy to a custom third party certificate
Mar 29, 2023 6:35:54 AM
Oct 29, 2014 7:39:47 AM
Content:
- About
- What is the current certificate used for?
- Certificate options, or: What type of certificate is right for me?
- Requirements, or: What to look out for when getting your cert.
- Where to get a certificate and how to do a CSR?
- Importing the Certificate
- The 5 Install Steps
- Step 1: Getting Started
- Step 2: Import the certificate
- Longer Step 2 (manual import):
- Step 3:Getting the Thumbprint
- Step 4:Configuring the Qlik Sense Proxy
- Step 5:Verification, or: How to prove the certificate was accepted.
- Related Content:
If you’ve just installed Qlik Sense Enterprise, then this image probably looks familiar. Alternatively, Chrome might display The site's security certificate is not trusted, while Firefox may report This Connection is Untrusted.
By default, Qlik Sense uses a self-signed certificate to enable HTTPS access across both the Hub (https:// YourSenseServer/hub) and the Management Console (https://YourSenseServer/qmc). But self-signed certificates cannot be validated or trusted by web browsers and tend to prompt a warning message.
To establish a secure HTTPS connection, the browser must trust the SSL/TLS certificate installed on the server. In the case of self-signed certificates, the signing Certificate Authority is not trusted, hence no certificates generated by the CA are trusted.
To install a trusted certificate for use with the Qlik Sense Enterprise on Windows Hub and Management Console, we need:
- An additional (signed) certificate.
- A brief (5 minute) downtime of the Qlik Sense Proxy.
These instructions are for replacing the certificate used for accessing the Qlik Sense Hub and Management Console. The certificate used for service communication cannot be replaced.
For video Transcript click here
About
What is the current certificate used for?
During the initial install, the Qlik Sense Repository Service creates a set of certificates. Their purpose is to secure Service Communication and Service Authentication.
Qlik Sense uses certificates to authenticate its service across all nodes. See the Qlik Sense Online Help for details. In addition, other products (such as Qlik NPrinting) require these certificates to be establish a connection.
This self signed certificate is then also used to secure hub and Management Console access through HTTPS.
We will not modify, replace, or remove the originally created certificates. Doing so will break service communication.
What we’ll do instead is to add an additional one.
Certificate options, or: What type of certificate is right for me?
There are three possible types of certificates for us to use.
- A certificate purchased from and signed by a trusted CA (Certificate Authority) such as VeriSign, Thawte, Geotrust, etc.
- A certificate provided and signed by your own Enterprise CA (Certificate Authority).
- And, of course, a self-signed one. Those can be created by any number of applications, such as Microsoft IIS, but is generally only recommended for test environments. More so, it has the potential side effect of teaching users to ignore browser warnings, which we do not want.
Requirements, or: What to look out for when getting your cert.
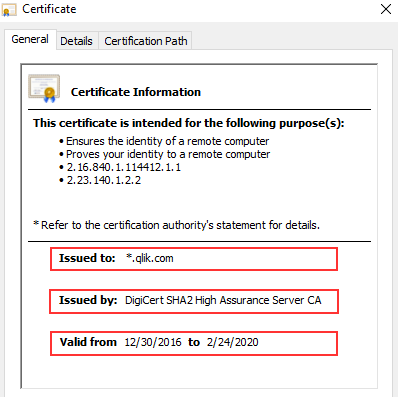
- The certificate must follow these requirements: Qlik Sense Enterprise on Windows: Compatibility information for third-party SSL certificates to use ...
- The certificate itself must contain a private key
- Has an up to date valid from / valid to date range
- Is signed by a valid and OS or browser configured Certificate Authority
When support gets questions, they are most often related to a certificate missing the private key. Always verify the certificate comes bundled with one when you install it.
It’ll look like this:
Where to get a certificate and how to do a CSR?
The Certificate Authority you chose will have instructions for this, and if you are looking to get a self-signed one or one from your corporation's CA, then a local administrator can provide the certificate to you.
Either way, you are going to need to generate a Certificate Signing Request (CSR) to pass on to your CA. There are tools out there to get that done with, such as certreq from Microsoft (found here), and SSLhopper has a great article on that, which I often send to customers when they ask us about CSRs and how to do them.
Once you obtain the certificate, we'll move on to installing it and activating it in Qlik Sense. This will be done in three quick steps:
- Import
- Get the Thumbprint
- Provide Thumbprint to the Proxy
Importing the Certificate
As mentioned before, we are not replacing certificates. The already existing ones will not be deleted. Doing so would break service authentication between the individual Qlik Sense services and render the system… broken.
The 5 Install Steps
Step 1: Getting Started
On the Qlik Sense node running the Qlik Sense Proxy, log on with the user running the Sense services. This is important since the certificate needs to be accessible for this account.
Step 2: Import the certificate
If the certificate was saved in the .pfx format, then all you need to do is double click the file. Follow the prompt to import the certificate into the Personal store.
Longer Step 2 (manual import):
If you want to import it manually or verify if it was correctly installed:
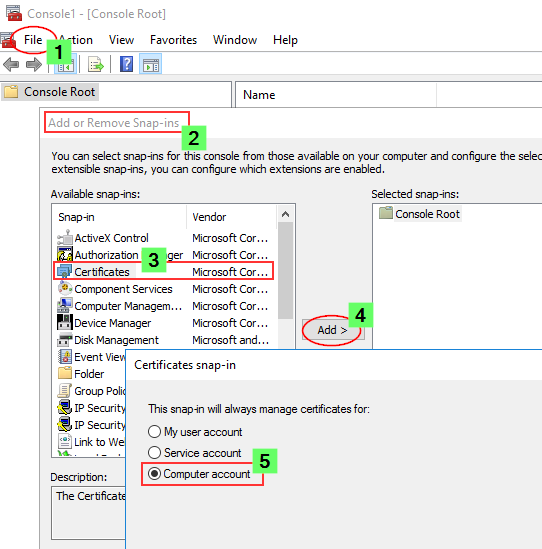
- Launch the Microsoft Management Console (mmc.exe) on the Proxy node
- In the MMC, go to File > Add / Remove Snap-in...
- Select Certificates and click Add
- Select Computer account, click Next, select Local computer and click Finish
- In the MMC, go to Certificates (Local Computer)/Personal
- In the MMC, go to Actions > All Tasks > Import...
- Browse to the certificate file provided to you from your CA
- Follow the instructions on the screen to import the certificate, including the private key
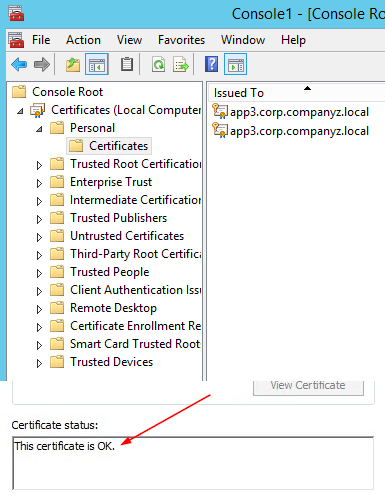
- Verify the new certificate has been imported into Certificates (Local Computer) > Personal > Certificates and that it contains a private key
- Double-click the Certificate > Certification Path and confirm it shows "This certificate is OK"
Step 3: Getting the Thumbprint
Well, since we are already in the MMC, let's open the freshly installed certificate again.
- Switch to the Details tab and scroll down until you find Thumbprint
- Mark the entire thing and copy it into, for example, Notepad.
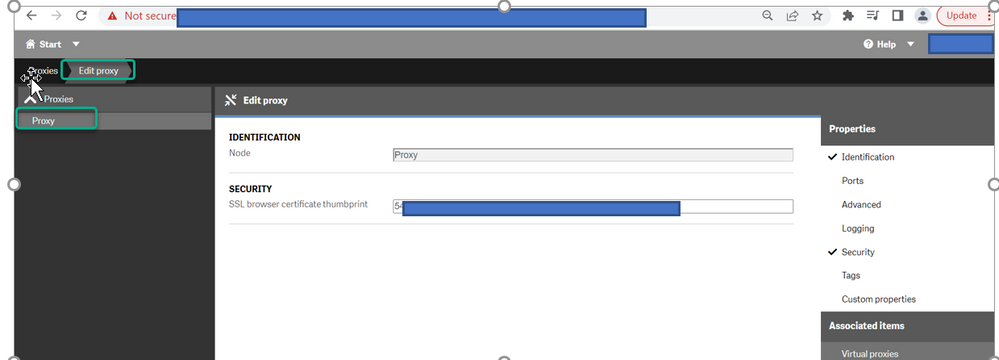
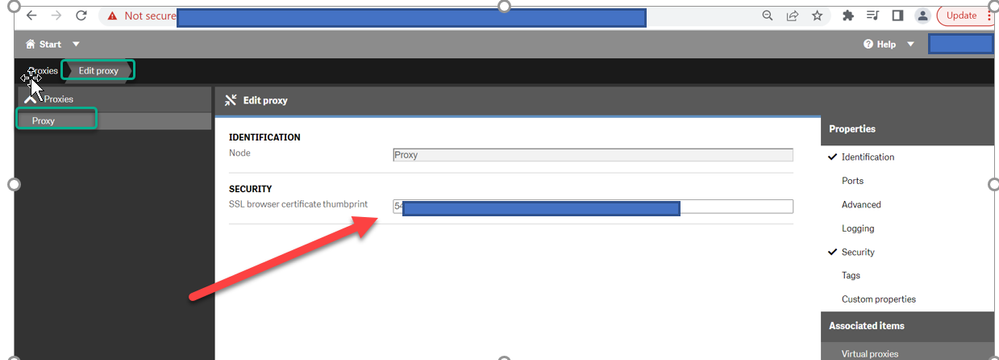
Step 4: Configuring the Qlik Sense Proxy
Almost done!
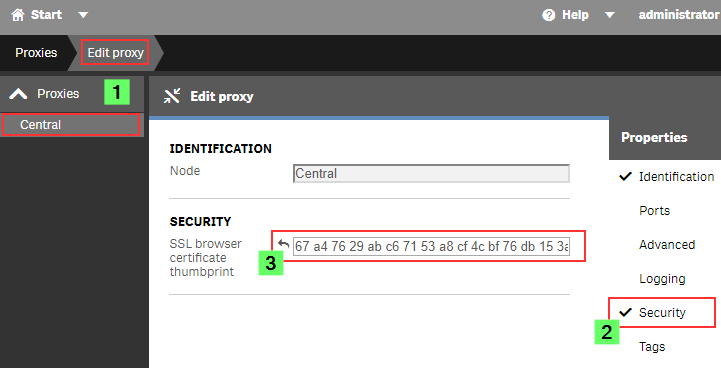
- Open the Qlik Sense Management Console (QMC)
- Go to Proxies
- Double click the Proxy you want to use (or select and choose Edit)
- Enable the Security options in the Properties panel on the right
- Paste the certificate Thumbprint into the SSL browser certificate thumbprint text box.
Click Apply.
The Sense Proxy will now restart. During the restart, it will be using Windows API calls to correctly bind the new certificate to its SSL ports.
Step 5: Verification, or: How to prove the certificate was accepted.
In the web browser:
When opening the Qlik Sense Hub or QMC, the certificate will now be displayed in the browser. This may look different depending on the web browser, but in Google Chrome you can click the padlock to the left of the URL to verify what certificate is used.
The information displayed needs to match the properties of the certificate you installed.
In the log files:
If you’d rather see what the Qlik Sense Proxy service is doing, then you can directly check up on that, too.
On the Proxy node, go to C:\ProgramData\Qlik\Sense\Log\Proxy\Trace and open the Security log file from just after the last start.
It will now print a slightly different message than before:
Security.Proxy.Qlik.Sense.Common.Security.Cryptography.LoggingDigester DOMAIN\_service Setting crypto key for log file secure signing: success
Security.Proxy.Qlik.Sense.Common.Security.Cryptography.SecretsKey DOMAIN\_service retrieving symmetric key from cert: success
Security.Proxy.Qlik.Sense.Common.Security.Cryptography.CryptoKey DOMAIN\_service setting crypto key: success
Security.Proxy.Qlik.Sense.Communication.Security.CertSetup 'CN=localhost' (08C871933A58E072FED7AD65E2DB6D5AD3EAF9FA) as SSL certificate presented to browser, which is a 3rd party SSL certificate
And that's it!
There isn't much more to it in a standard Qlik Sense Enterprise installation, but if you have more questions, then maybe a few of these articles can help:
Receiving Bad Request 400?
Make sure the URL/FQDN you are using to access the Hub and QMC is correctly added to the WebSocket Allow List: How to configure the WebSocket origin allow list and best practices
I applied my certificate and it seems to be using it correctly, but browsers are still saying the Common Name is Invalid?
ERR_CERT_COMMON_NAME_INVALID when using 3rd party certificate
Qlik Sense keeps reverting to the default and complains it can't find a valid ssl certificate with the thumbprint.
The certificate may not have a Private key or the service account does not have access to it.
How to: Manage Certificate Private Key
The Qlik Sense Service account doesn't have admin privileges and the certificate is not accepted.
Related Content:
- Qlik Sense Hub and QMC with custom SSL certificate
- A certificate error or warning is displayed in the browser when accessing the Qlik Sense Hub or Mana...
- Qlik Sense - Changing to a signed server proxy certificate
- Qlik Sense - Changing a proxy certificate
- ERR_CERT_COMMON_NAME_INVALID when using 3rd party certificate
- Qlik Sense: Compatibility information for third-party SSL certificates to use with HUB/QMC
- Requirements for configuring Qlik Sense with SSL
- Couldn't find a valid ssl certificate with thumbprint and the incorrect certificate used on hub
- How to: Change the Qlik Sense Proxy certificate if the service account does not have local administr...
- NET::ERR_CERT_AUTHORITY_INVALID
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
@gdrabla we have similar situation with security scans - you will likely just have to provide documentation to your security team from Qlik, that these self signed certificates are just for INTERNAL communication and that as @Sonja_Bauernfeind is stating, there is no option to change that at all.
this pdf is a good starting point
(Qlik Sense use of certificates Architectural overview)
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
@Sonja_Bauernfeind - Thank you for reply, much appreciated. Few more questions -
Please note i'm learning QLIK being new user , still trying to understand architecture design. bear for me asking few more questions.
Question # 1 - Is it possible for you to pick up the QLIK Case directly & have screen session with me ?. We have support account with QLIK. If answer is yes - i will share create QLIK case via offline message.
Question # 2 - I'm still not clear on answer for below , please find the comments for below answer:
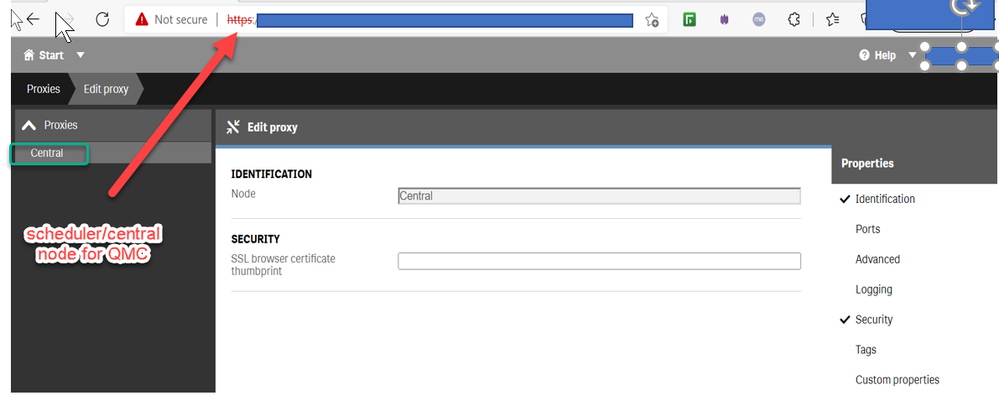
Question - Which Proxy choose Central or Proxy for updating Thumbprint?
If you still wish to change the certificate used for hub and qmc access, choose the proxy which is hosting your users.
We have one proxy node(web01) from where users can access to QMC and HUB also. Also we have Central node in case if proxy goes down then user can access QMC and HUB from central node. Currently our certificate on scheduler node is not secure that's reason we have vulnerability scan on port 443. We are planning to update certificate on scheduler node.
Question here - Do we need update the thumbprint from new certificate on Proxy/or QMC Link - https://<schedulernode>/qmc . Currently its updated on Proxy which might be incorrect so thought to check with you.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hello @gdrabla
As you have multiple proxy nodes, you will need to:
- Install the certificate on each node with a proxy
- Then change/add the thumbprint on each node
I have replied to your direct message regarding the support request.
All the best,
Sonja
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hello @Sonja_Bauernfeind ,
I will followed the steps , will keep you posted about same. Fingers crossed.
- Open the Qlik Sense Management Console (QMC)
- Go to Proxies
- Double click the Proxy you want to use (or select and choose Edit) <-- I will select Proxy on scheduler/central node as below .
- Enable the Security options in the Properties panel on the right
- Paste the certificate Thumbprint into the SSL browser certificate thumbprint text box.
- Click Apply.
- The Sense Proxy will now restart. During the restart, it will be using Windows API calls to correctly bind the new certificate to its SSL ports.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
I had similar issue while importing wild card certificate. The issue was related to folder, we had to import certificate in Personal folder instead of trusted root certificate.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
After successfully installing a trusted certificate I am unable to access my QMC any longer. I believe its because I copied the Thumbnail from the new certificate to the Proxy of the Central node, any advice pls. (self managed windows Ent) Desperate to get back to QMC
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hello @Bamendaboyplus
Replacing the certificate thumbnail will not break the connection to the QMC. If it is incorrect, Sense will simply revert back to its self-signed certificate. Can you provide us with more information on the error you are seeing in the QMC as well as what is being logged? You can review the log files here: C:\ProgramData\Qlik\Sense\Log\.
It may be necessary for us to redirect this conversation to the forums for further troubleshooting or for a ticket to be logged.
All the best,
Sonja
- « Previous
- Next »