Unlock a world of possibilities! Login now and discover the exclusive benefits awaiting you.
Search our knowledge base, curated by global Support, for answers ranging from account questions to troubleshooting error messages.
Recent Documents
-
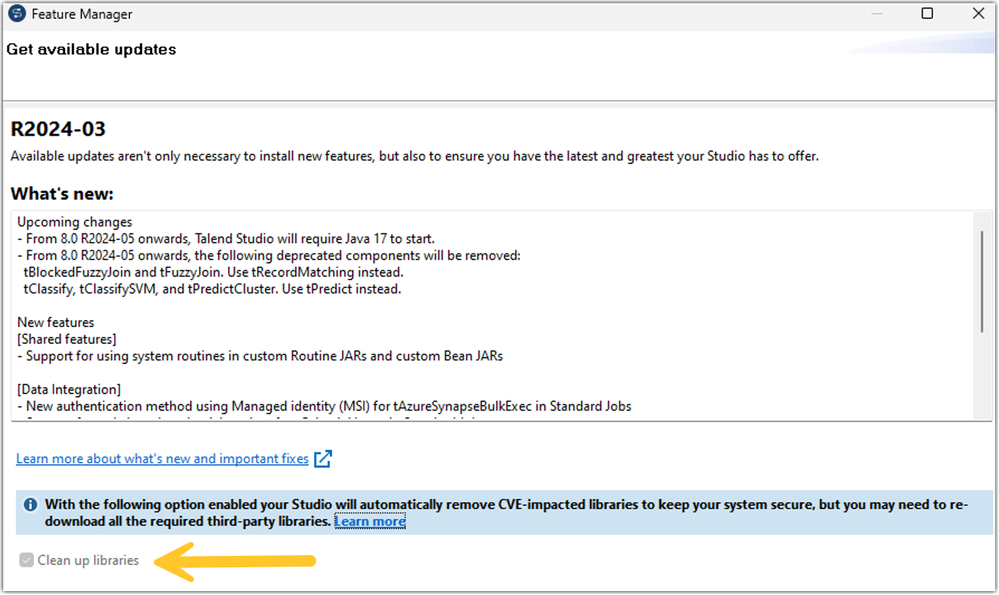
Qlik Talend Studio: "Clean up Libraries" check box greyed out when patching fro...
When patching Studio from the Feature manager, the Clean up libraries option is greyed out: Resolution Navigate to <Talend Studio Home>\studio\ Ba... Show MoreWhen patching Studio from the Feature manager, the Clean up libraries option is greyed out:
Resolution
- Navigate to <Talend Studio Home>\studio\
- Backup and edit Talend-Studio-win-x86_64.ini (Win OS) or Talend-Studio-macosx-cocoa.ini (Mac OS)
- Remove the following parameter -Dtalend.studio.m2.clean=true
- Save and restart Studio
Cause
The -Dtalend.studio.m2.clean=true property ensures Studio removes obsolete jars during patching.
Related Content
For more information, please review the Studio installation guide.
Environment
Talend Studio 8.0.1
-
QlikView HSTS (HTTP Strict-Transport-Security response header)
HSTS (HTTP Strict-Transport-Security response header) security check failed. HTTP Strict Transport Security (HSTS) is a policy mechanism that helps to... Show MoreHSTS (HTTP Strict-Transport-Security response header) security check failed.
HTTP Strict Transport Security (HSTS) is a policy mechanism that helps to protect websites against man-in-the-middle attacks such as protocol downgrade attacks and cookie hijacking. It allows web servers to declare that web browsers (or other complying user agents) should automatically interact with it using only HTTPS connections, which provide Transport Layer Security (TLS/SSL), unlike the insecure HTTP used alone.
Resolution
Before adding HSTS to either the QlikView AccessPoint or the QlikView Management Console (QMC), set both up to use HTTPS. See for QlikView AccessPoint and QMC with HTTPS and a custom SSL certificate instructions.
HSTS for the QlikView AccessPoint
Custom response headers can be set in both the QlikView WebServer (beginning with 12.30) and Microsoft IIS (all QlikView versions).
The custom header needed for HSTS is: Strict-Transport-Security
- Run text editor (e.g. Notepad) as Administrator
- Edit QlikView WebServer configurations file. The default path is C:\ProgramData\QlikTech\WebServer\config.xml
- Locate CustomHeaders element within the config file. For more information, see QlikView WebServer: Custom HTTP Header.
- Add custom response header as <Header> element(s) with sub-elements defining Strict-Transport-Security as the name and your desired max-age= as value.
Example:<Config> ... <Web> ... <CustomHeaders> <Header> <Name>Strict-Transport-Security</Name> <Value>max-age=31536000</Value> </Header> </CustomHeaders> </Web> </Config> - Restart QlikView WebServer service
For information on how to configure custom headers with Microsoft IIS, see Setting Custom HTTP Headers in IIS for QlikView. The site https://https.cio.gov/hsts/ gives information on how to setup the webserver to enable HSTS.
Testing can be achieved using any number of third party sites, such as:HSTS for the QlikView Management Console (QMC)
This setting was introduced with QlikView 12.70 (May 2022) SR1.
QVManagementService.exe.Config Changes:
- Stop the QlikView Management Services
- Go to ProgramFiles => qliktech => management service => open QVManagementService.exe.config using an administrator notepad
- Update this value to true =>
<add key="UseHSTS" value="true" /> - To enable HSTS to header this value has to be set to true
<add key="UseHTTPS" value="true" />
Environment:
- Run text editor (e.g. Notepad) as Administrator
-
High Severity Security fix for QlikView (CVE-2024-29863)
Executive Summary A security issue in QlikView has been identified and patches have been made available. In both cases, a user with existing access t... Show MoreExecutive Summary
A security issue in QlikView has been identified and patches have been made available. In both cases, a user with existing access to the Windows environment running QlikView or the QlikView plugin may be able to escalate their privileges to that of Administrator.
The issue was identified and responsibly reported to Qlik by Pawel Karwowski and Julian Horoszkiewicz from Eviden Red Team.
Qlik has received no reports of these vulnerabilities being exploited maliciously.
Affected Software
All versions of QlikView prior to and including the following releases are impacted:
- QlikView May 2023 SR1 (12.80.20100)
- QlikView May 2022 SR2 (12.70.20200)
Vulnerability Details
CVE-2024-29863 (QV-25113)
Severity: CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:C/C:H/I:H/A:H (7.8 High)
A race condition exists in the QlikView installer executable that may allow an existing lower privileged user to cause code to be executed in the context of a Windows Administrator.
Resolution
Recommendation
Customers should upgrade QlikView to a version containing fixes for these issues. Fixes are available for the following versions:
- QlikView May 2023 SR2 (12,80.20200)
- QlikView May 2022 SR3 (12.70.20300)
Credits
Pawel Karwowski and Julian Horoszkiewicz from Eviden Red Team.
-
Qlik Sense Enterprise on Windows: Securing and Hardening Server
Security of Qlik Sense Enterprise on Windows can be approached in the below discrete areas. All these areas provide different options for increasing s... Show MoreSecurity of Qlik Sense Enterprise on Windows can be approached in the below discrete areas. All these areas provide different options for increasing security in a deployment, and thereby mitigating vulnerabilities and protecting against attackers.
Content:
- 1. Authentication
- 2. Authorization
- Security Rules
- Section Access
- 3. Operating System Hardening
- Step 1: Disabling protocols and ciphers
- Step 2: Firewalls
- Step 3: Service Account Permission
- Step 4: Anti-Virus
- Step 5 (Optional): FIPS
- 4. PostgreSQL Hardening
- 5. Generalized Web Server best practices
- Apply a trusted certificate
- Optional: Additional HTTP Response Headers
Be aware that a high level of server hardening can lead to failure in your deployment. Be mindful of always having a backup to restore to in case your configuration leads to irreversible failure.
1. Authentication
Qlik Sense Enterprise on Windows supports multiple different Authentication Solutions;
- Windows (NTLM)
- Kerberos
- Ticketing
- SAML
- JWT
- Header
- Anonymous
Qlik can not specify which authentication method is appropriate for each deployment. It is advisable to review currently supported alternatives within your organization and/or Identity Provider (IdP) to implement the most suitable solution for your use case.
2. Authorization
Qlik Sense Enterprise on Windows provides two levels of native authorization in the product.
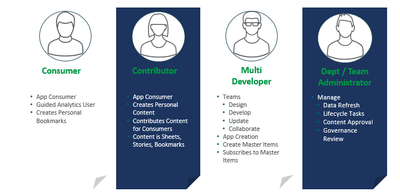
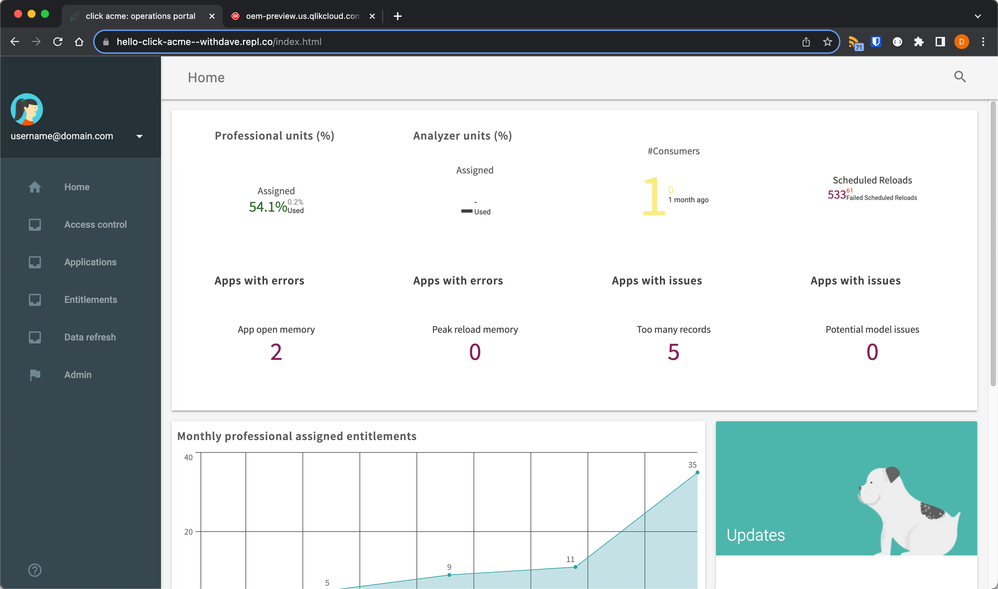
Security Rules
Attribute based access control (ABAC), which is configured through Qlik Sense security rules. This article will not go in depth on how to best implement security rules for your requirements, but it is highly recommended to think of your users based on the capabilities that you intend to provide them. For example different roles and capabilities as shown in image below, allows for a security rule framework to be designed and implemented. This can be done either by yourself by referencing Qlik Sense Help for Administrators and available assets or by engaging with a Qlik Consultant or Qlik Partner.
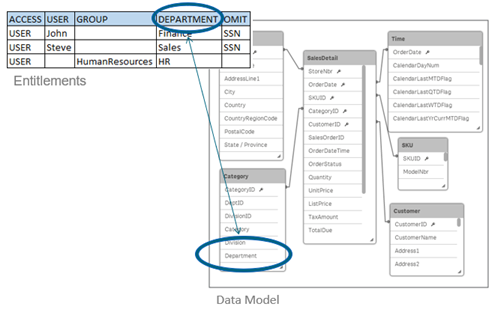
Section Access
Row level data reduction, which is configured through Section Access at Qlik Sense app level. This article will not go in depth on Section Access implementation, but with this reduction a single file can be used to hold the data for a number of users or user groups. Qlik Sense uses the information in the section access for authentication and authorization, and dynamically reduces the data, so that users only see their own data.
3. Operating System Hardening
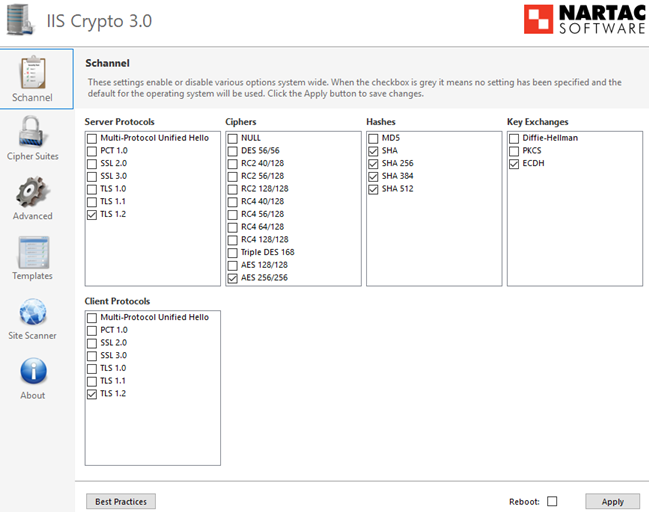
Qlik Sense Enterprise on Windows inherits the available protocols, cipher suites, key exchanges and other security hardening which are enabled on the Windows Server operating Qlik Sense.
Step 1: Disabling protocols and ciphers
Windows Server has a lot of protocols enabled by default; however protocols, ciphers, hashes and key exchanges that are considered deprecated or not secure enough should be disabled. There are many ways of doing this, and the Windows administrator and security experts should be consulted so that local policies are accurately applied. For simplicity, understanding and a good overview IIS Crypto 3.0 can be a good tool for evaluating current Windows configuration and applying changes.
Keep in mind that "Best Practice" today might not be recommended in the near future, what was considered "safe" a while ago is not necessarily considered so today. For this reason, it is also important to regularly scan servers for potential vulnerabilities and revisit configurations as required.
Windows Server needs to be restarted for these settings changes to take effect. It is also important to ensure that all components running on the server still operate as expected after hardening is applied, for example older non-Qlik software might not be compliant with the latest options and standards.Step 2: Firewalls
Firewalls typically should be closed, with required ports only opened for intended purposes.
See Qlik Sense Enterprise on Windows ports overview for details on required port based on the deployed architecture.Step 3: Service Account Permission
For most organizations, local administrator rights allow for an easier deployment, but Qlik Sense Enterprise on Windows does not require local administrator rights in order to function. This can be an attractive option inside some organizations. This will require additional configuration of boot strap mode as described in Qlik Sense Enterprise on Windows Services.
For a brief overview of the rights needed by a Qlik Sense Enterprise service account:- Full control over the share used by Qlik Sense Enterprise
- Full control over the installation directory (default: C:\Program Files\Qlik)
- Full control over %ProgramData%\Qlik
- Full control over any folders used as data connections
Qlik Sense Enterprise for Windows does not officially support Group Managed Service Accounts (gMSA), but it can operate using one. The initial barrier is that the installer requires a service account and password to be entered during installation. A domain or local account could be substituted for the install stages only to be swapped out in the Windows Services applet (services.msc) after installation. Some functionality may require workarounds (e.g. A User Directory Connection to Active Directory).
Step 4: Anti-Virus
Qlik Sense Enterprise on Windows does require exceptions from anti-virus scan to avoid potential disk I/O conflicts. Refer to Qlik Sense Folder And Files To Exclude From AntiVirus Scanning for more details.
Step 5 (Optional): FIPS
Qlik Sense Enterprise on Windows can run with Federal Information Processing Standards (FIPS) enabled on the Windows Server. This does require a few adjustments of configuration files due to Qlik using non-FIPS compliant algorithms for minor tasks like hash checks. See Running Qlik Sense on Windows systems with FIPS compliance enabled for more details on Qlik Sense and FIPS.
4. PostgreSQL Hardening
Qlik Sense Enterprise on Windows uses PostgreSQL to store meta-data relating to a Qlik Sense site. In multi-node sites or sites where PostgreSQL is isolated from Qlik Sense Enterprise for Windows additional security can be applied;
- Database Traffic Encryption
- Hardening what endpoints are allowed to connect to PostgreSQL as described in PostgreSQL: postgresql.conf and pg_hba.conf explained
5. Generalized Web Server best practices
Qlik Sense Proxy service bundled with Qlik Sense Enterprise on Windows is simply a web-service. This means applying general practice guidance but in the context of Qlik Sense as described below.
Apply a trusted certificate
Qlik Sense Enterprise on Windows acts as a Certificate Authority (CA) during initial installation and signs a certificate that is applied on all encrypted traffic between Qlik Sense services. The same Qlik Sense signed certificate is applied as default certificate also for incoming connections from users accessing Qlik Sense Hub and QMC. This default certificate is not intended for production use, unless user access to Qlik Sense comes through a network load balancer or reverse proxy that trusts the Qlik Sense certificate. For direct user access to Qlik Sense Proxy, a fully trusted certificate can typically be acquired from your local IT and then applied on the Qlik Sense Proxy service.
As of July 2019, Qlik Sense Enterprise on Windows support SHA1 and SHA2 certificates. If SHA384 or SHA512 certificates are needed, then a network load balancer or reverse proxy can be configured in front of Qlik Sense which offloads to Qlik Sense.
Optional: Additional HTTP Response Headers
There are numerous HTTP response headers that can be used in attempting to secure a server. Below are a couple of the most common ones, but as always it is recommended to consult local IT and web security expert on what the recommendations are.
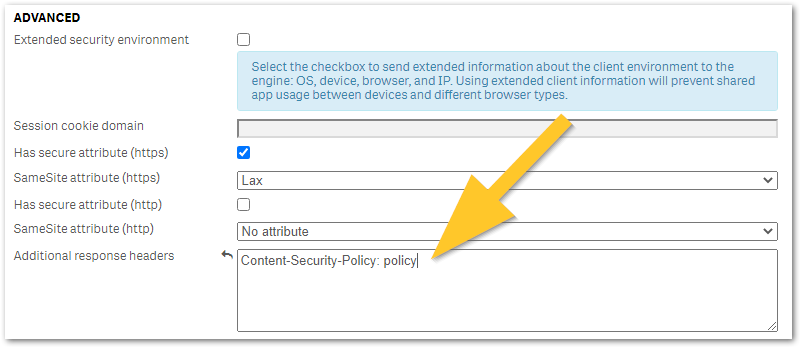
Any additional HTTP response header values can be configured in Qlik Sense Virtual Proxy settings under Additional response headers as shown in the below image and described in Qlik Sense for Administrators: Virtual Proxies. It is recommended to trial any header changes in a new virtual proxy, as poor configuration may accidentally lock you out from Qlik Sense access.
- HTTP Strict Transport Security (HSTS) HTTP Strict Transport Security (HSTS) is an opt-in security enhancement which any web application can support through the use of a special response header. When a supported browser receives this header that browser will prevent any communication sent over HTTP in the future and will redirect all traffic over HTTPS instead. Caution is advised when implementing HSTS, as it might block HTTP access to certain pages that actually requires it or needs to be excluded from HSTS. See MDN Web Docs: Strict-Transport-Security for more details on configuration options.
- Optional: X-Content-Type-Options X-Content-Type-Options response HTTP header is a marker used by the server to indicate that the MIME types advertised in the Content-Type headers should not be changed and be followed. This allows to opt-out of MIME type sniffing.
- X-Frame-Options will prevent the site to be embedded in an iFrame, which can effective mitigate against ClickJacking attacks
- Content-Security-Policy: policy (old: X-XSS-Protection) improves security against some types of XSS (cross-site scripting) attacks.
Policy is a placeholder for your policy of choice and cannot be used as a value. See Writing a Policy (Mozilla) for examples.
-
Qlik Sense Enterprise on Windows: Compatibility information for third-party SSL ...
A third-party certificate was configured in the Qlik Sense Proxy, but is not being used. The connection is not private" NET::ERR_CERT_COMMON_NAME_INVA... Show MoreA third-party certificate was configured in the Qlik Sense Proxy, but is not being used.
The connection is not private" NET::ERR_CERT_COMMON_NAME_INVALID may be displayed on HUB access.
Qlik Sense Enterprise on Windows uses self-signed and self-generated certificates to protect communication between services, as well as user web traffic to the hub and management console. It is possible to use a third-party-issued SSL certificate to protect client web traffic. Using the self-signed certificate will cause a certificate warning to be displayed in the web browser (such as Google Chrome or Internet Explorer).
If the third-party certificate for the Qlik Sense Proxy Service is not fully compatible with Qlik Sense or it does not have the correct attributes and cyphers, the Qlik Sense Repository Service will revert to using the default certificates. The following error may occur in the Proxy Security logs:
Example: C:\ProgramData\Qlik\Sense\Log\Proxy\Trace\HOSTNAME_Security_Proxy.txtNo private key found for certificate 'CN=qliksense.domain.com' ([CERTIFICATE THUMBPRINT HERE]) Couldn't find a valid ssl certificate with thumbprint [CERTIFICATE THUMBPRINT HERE] Reverting to default Qlik Sense SSLCertificate Set certificate 'CN=qliksenseserver1.domain.com' ([CERTIFICATE THUMBPRINT HERE]) as SSL certificate presented to browser
Resolution:
In order for Qlik Sense Enterprise to correctly recognize the third-party certificate as valid, the certificate will have to meet the following requirements:
Note: Root and Intermediate CA certificates need to be correctly installed. Should any be missing, Qlik Sense proxy will not use the server certificate and will revert back to using the self-signed certificate instead.
Certificates that are known to work well with Qlik Sense have the following attributes:- Certificates that are x509 version 3. More information including filename extensions under https://en.wikipedia.org/wiki/X.509
- Use signature algorithm sha256RSA
- Use signature hash algorithm sha256
- Signed by a valid, and OS/browser configured , CA
- Are valid according to date restrictions (valid from/valid to)
- Key in format CryptoAPI (not in CNG)
- The certificate itself has to contain private key no matter what Qlik Sense version.
Related Content:
How to: Change the certificate used by the Qlik Sense Proxy to a custom third party certificate
-
Qlik Cloud: Content restricted or unavailable with Embedded Analytics User role ...
The Embedded Analytics User role is a role available in Qlik Cloud for use cases where your users should not access the Qlik Cloud hub directly. If t... Show More -
Qlik Replicate and PostgreSQL source endpoint: DDL operation fails with ERROR: p...
The PostgreSQL source endpoint is set up with a privileged account (account with a superuser role) used in the source endpoint connection. After the ... Show MoreThe PostgreSQL source endpoint is set up with a privileged account (account with a superuser role) used in the source endpoint connection. After the task's first successful run, all of the regular user (account without a superuser role) cannot perform any DDL operations in the database,regardless if the table is included in the replication task or not, or even create a new table. Below errors will show up upon any DDL operation.
In the meanwhile, DML operations continue to work; the INSERT/UPDATE/DELETE changing records can be captured and applied to target sides successfully.
Errors:
ERROR: permission denied for table attrep_ddl_audit. The SQL statement 'insert into public.attrep_ddl_audit values ...'.
Resolution:
There are two alternatives. Apply one.
Pros and Cons:
-
Update permissions. This is a straightforward but potentially work-intensive solution. Give all regular users who need to run tasks the required permissions.
-
Execute the function definition with "security definer" option by a privileged account. While this option is simpler, it must be performed carefully as not to enable misuse.
Update permissions
In this scenario Qlik Replicate is in fact using the default option "security invoker" in function definition.
Grant the following permissions to the non-privileged account, see Qlik Replicate User Guide:GRANT INSERT ON attrep_ddl_audit to <non-privileged-user>;
GRANT DELETE ON attrep_ddl_audit to <non-privileged-user>;
GRANT USAGE ON attrep_ddl_audit_c_key_seq TO <non-privileged-user>;Security definer and privileged account
WARNING! Writing SECURITY DEFINER Functions Safely
Because a SECURITY DEFINER function is executed with the privileges of the user that owns it, care is needed to ensure that the function cannot be misused. For security, search_path should be set to exclude any schemas writable by untrusted users.Execute the function definition with "security definer" option by a privileged account, for example an account with superuser privilege. See the complete function definition code is as below.
The code is generated by Qlik Replicate 2023.5, only "security definer" option is added manually.
-- DROP FUNCTION public.attrep_intercept_ddl();CREATE OR REPLACE FUNCTION public.attrep_intercept_ddl()RETURNS event_triggerLANGUAGE plpgsql security definerAS $function$declare _qry text;BEGINif (tg_tag='CREATE TABLE' or tg_tag='ALTER TABLE' or tg_tag='DROP TABLE' or tg_tag='TRUNCATE') thenSELECT current_query() into _qry;insert into public.attrep_ddl_auditvalues(default,current_timestamp,current_user,cast(TXID_CURRENT()as varchar(16)),tg_tag,0,'',current_schema,_qry);delete from public.attrep_ddl_audit;end if;END;$function$;This customization is provided as is. Qlik Support cannot provide continued support for the solution. For assistance, reach out to your DBA and/or PostgreSQL related services.
Internal Investigation ID(s):
#00021532, #00123792
Environment:
- Qlik Replicate All versions
- PostgreSQL All versions ("security definer" was introduced from version 8.0)
-
-
Qlik Sense authentication fails with X509N Bad User Name - Login Failures
The Windows Security Event log reports the following event: event ID 4768, Task Category "Kerberos Authentication Service". Account name for these ent... Show MoreThe Windows Security Event log reports the following event:
event ID 4768, Task Category "Kerberos Authentication Service". Account name for these entries will be "X509N:<S>CN=QlikClient
Resolution:
Without a Multi-Cloud/Hybrid setup
If you are a customer currently not using a Multi-Cloud/Hybrid setup, meaning you are not distributing Apps from Client Managed into SaaS.
Option 1:
- Stop the Qlik Sense Services
- Open the following path: C:\Program Files\Qlik\Sense\Repository\
- Open Repository.exe.config
- Set "EnableDotNetWebSockets" to true.
- If the Qlik Services are running using a non-local administrator account, then bootstrapping needs to be run after the changed configuration. The fix is not supported by Windows 7.
Option 2:
It is possible that the error is still seen after option one is applied. It is found that due to the current architecture following services are triggering the error:
[hybriddeploymentservice]
[appdistributionservice]
[qib-webchat-service]If the Qlik Sense environment is not using Multi-cloud deployment, you may apply the following workaround by disabling the following two services:
[hybriddeploymentservice]
[appdistributionservice]To do this:
- Open the file "services.conf" of the Qlik Sense installations (it is typically located at C:\ProgramFiles\Qlik\Sense\Ser
viceDispatcher). - Make a backup of "services.conf" file first
- Go to the section defining the service in question by adding the row "Disabled=true" like this:
[hybriddeploymentservice]
Disabled=true
Identity=Qlik.hybrid-deployment-service
DisplayName=Hybrid Deployment Service
ExePath=dotnet\dotnet.exe UseScript=false
[appdistributionservice]
Identity=Qlik.app-distribution-service
DisplayName=App Distribution Service
ExePath=dotnet\dotnet.exe
UseScript=false - The "Qlik Sense Service Dispatcher" service needs to be restarted for the setting to take effect.
If you are not using Qlik Webchat, you can also disable
[qib-webchat-service]by following same steps as above.With a Multi-Cloud/Hybrid setup
If you are a customer currently using a Multi-Cloud/Hybrid setup, meaning you are distributing Apps from Client Managed into SaaS.
With a multi-cloud setup, there is no complete workaround available as of today. It is important to mention that this is not an issue that affects in any way your security and/or stability of your Client Managed deployment. This is a result of how affected Qlik Sense .NET microservices are handling certificates in .NET Core technology. To address this shortcoming, a significant re-design of current architecture would be required that is currently not in the pipeline, hence would recommend submitting a product ideation.
To limit the number of events in question, if you are not using Qlik Webchat, you can disable
[qib-webchat-service]- see step-by-step instructions in the previous section.Environment:
Qlik Sense Enterprise on Windows
Internal Investigation ID(s):
QLIK-87774, QB-274. Working as intended, please apply the resolution given in this article.
-
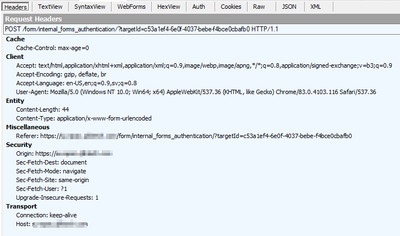
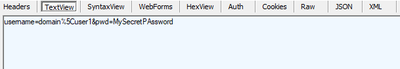
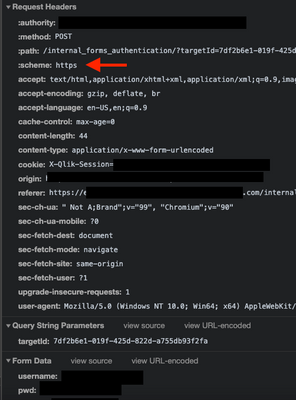
Vulnerability Concern: Username and password sent in plain text
A penetration test shows traffic traces between a client device and a server that reveals the user's credentials. This might be flagged as a potentia... Show More -
Critical Security fixes for Qlik Sense Enterprise for Windows (CVE-2023-48365)
Executive Summary A security issue in Qlik Sense Enterprise for Windows has been identified, and patches have been made available. If successfully ex... Show MoreExecutive Summary
A security issue in Qlik Sense Enterprise for Windows has been identified, and patches have been made available. If successfully exploited, this vulnerability could lead to a compromise of the server running the Qlik Sense software, including unauthenticated remote code execution (RCE). This resolves an incomplete fix for CVE-2023-41265.
This issue was identified and responsibly reported to Qlik by Adam Crosser and Thomas Hendrickson of Praetorian.
Qlik has received reports that this vulnerability may be being used by malicious actors. Customers should confirm they have applied the necessary patches outlined in this bulletin. If there are additional questions, customers may log a case with Qlik Support.
Affected Software
All versions of Qlik Sense Enterprise for Windows prior to and including these releases are impacted:
- August 2023 Patch 1
- May 2023 Patch 5
- February 2023 Patch 9
- November 2022 Patch 11
- August 2022 Patch 13
- May 2022 Patch 15
- February 2022 Patch 14
- November 2021 Patch 16
Severity Rating
Using the CVSS V3.1 scoring system (https://nvd.nist.gov/vuln-metrics/cvss), Qlik rates this severity as critical.
Vulnerability Details
CVE-2023-48365 (QB-21683) HTTP Tunneling vulnerability in Qlik Sense Enterprise for Windows
Severity: CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:C/C:H/I:H/A:N (9.6 Critical)
Due to improper validation of HTTP Headers a remote attacker is able to elevate their privilege by tunnelling HTTP requests, allowing them to execute HTTP requests on the backend server hosting the repository application. This resolves an incomplete fix for CVE-2023-41265.
Resolution
Recommendation
Customers should upgrade Qlik Sense Enterprise for Windows to a version containing fixes for these issues. Fixes are available for the following versions:
- November 2023 IR
- August 2023 Patch 2
- May 2023 Patch 6
- February 2023 Patch 10
- November 2022 Patch 12
- August 2022 Patch 14
- May 2022 Patch 16
- February 2022 Patch 15
- November 2021 Patch 17
These patches include the fixes for previous issues CVE-2023-41266 and CVE-2023-41265 (link).
All Qlik software can be downloaded from our official Qlik Download page (customer login required).
Edit December 1st, 2023: Added November 2023 IR release to clarify it is not affected
-
Qlik Security Vulnerability Policy
Does Qlik have a defined security policy?Qlik takes the security of our products seriously. We have a dedicated team of security experts working on t... Show MoreDoes Qlik have a defined security policy?
Qlik takes the security of our products seriously. We have a dedicated team of security experts working on testing, hardening and securing our products. We also work closely with external security companies, our customers and partners to ensure the security of our products is of the highest standard.
Our Qlik Trust and Compliance Center provides details for compliance and security questions across all Qlik products.What do I do if I find a security vulnerability in a Qlik product?
Please report any security vulnerability concern to Qlik Support. For an accurate an detailed evaluation of a potential security vulnerability, it is important to clear describe the scenario in which a vulnerability has been exposed. This includes describing the steps for how security is compromised and what detail can be exposed by an attacker.
Notice, that generic test reports from 3rd auditing tools typically do not include detailed steps of vulnerability exposure in their security report. These reports commonly referring to potential risk based patterns, they do not actually expose a vulnerability as part of their system evaluation. Consequently this means that the default report details are not enough for Qlik to take any immediate action on based on the raised concern. Please consult 3rd party security auditor or local security expert for complete test case details before reporting support case with Qlik.To enable qualified and efficient investigation and action by Qlik, please report each vulnerability concern as an individual support case with Qlik Support. This means that each concern raised in a 3rd party test report must be reported as a separate support case.
For each case consider adding as much detail as possible, in line with below items:- Qlik product name
- Qlik product version
- Test case subject/name (if based on test report)
- Complete penetration test report (attach full report for reference)
- Name of security tool used for testing
- Details of how to replicate the vulnerability
- Step by step description on how to expose vulnerability
- Recording of reproduction
- Supporting material, e.g. logs, traffic traces or screenshots
- Vulnerability impact
- Type of information exposed
- Unauthorized access to content
- CVSS score if provided by security auditor
-
Qlik Sense Enterprise on Windows: PostgreSQL vulnerabilities CVE-2023-2454 and C...
PostgreSQL has identified two security issues. As Qlik Sense Enterprise on Windows relies on PostgreSQL for its repository, we want to provide you wit... Show MorePostgreSQL has identified two security issues. As Qlik Sense Enterprise on Windows relies on PostgreSQL for its repository, we want to provide you with steps on how to mitigate the vulnerabilities.
- CVE-2023-2454
This enabled an attacker having database-levelCREATEprivilege to execute arbitrary code as the bootstrap superuser. Database owners have that right by default, and explicit grants may extend it to other users. - CVE-2023-2455
While CVE-2016-2193 fixed most interaction between row security and user ID changes, it missed a scenario involving function inlining. This leads to potentially incorrect policies being applied in cases where role-specific policies are used and a given query is planned under one role and then executed under other roles. This scenario can happen under security definer functions or when a common user and query is planned initially and then re-used across multipleSET ROLEs. Applying an incorrect policy may permit a user to complete otherwise-forbidden reads and modifications. This affects only databases that have usedCREATE POLICYto define a row security policy.
Resolution
With the next major Qlik Sense Enterprise on Windows release (August 2023), Qlik will update its bundled PostgreSQL database to the latest 14.x version.
As a mitigation for any previous releases, including May 2023, we offer the Qlik Postgres Installer (QPI) to migrate from 9.6 or 12.5 embedded databases to 14.8. We validated PostgreSQL 14.x for all releases back to February 2022.
Download the Qlik Postgres Installer versions 1.3.0 here.
There are two possible scenarios which may apply to you:
Scenario 1
Upgrading your PostgreSQL database for Qlik Sense February 2022 (or later) while not having used the QPI yet
Use the new Qlik Postgres Installer (version 1.3.0) to upgrade to Postgres 14.8 and migrate Postgres with QPI. Follow the instructions in Upgrading Qlik Sense Repository Database using the Qlik PostgreSQL Installer.
Download the Qlik Postgres Installer versions 1.3.0 here.
Scenario 2
Upgrading your PostgreSQL on February 2022 (or later) if you have already migrated to 12.x within QPI
If you have previously used the Qlik Postgres Installer (version 1.2.1 or earlier), you can simply install the latest PostgreSQL version (within your major release) and install it on top of your current 12.x database.
Steps:
- Download the latest PostgreSQL installer within the major release you have installed (Download PostgreSQL | Enterprisedb.com).
Example: You have used the old QPI to upgrade to 12.5. You can now easily upgrade to a later version in the same major release, such as 12.15. - Stop the Qlik Sense services. Leave the postgresql-x64-12 service running.
- Run the downloaded installer as an administrator.
- The installer will guide you through the upgrade procedure.
- Start the Qlik Sense services.
Related Content
https://www.cybersecurity-help.cz/vdb/SB2023051138
Download PostgreSQL | Enterprisedb.comEnvironment
Qlik Sense Enterprise on Windows all versions
- CVE-2023-2454
-
Critical Security fixes for Qlik Sense Enterprise for Windows (CVE-2023-41266, C...
Executive Summary Two security issues in Qlik Sense Enterprise for Windows have been identified and patches made available. If the two vulnerabilitie... Show MoreExecutive Summary
Two security issues in Qlik Sense Enterprise for Windows have been identified and patches made available. If the two vulnerabilities are combined and successfully exploited, these issues could lead to a compromise of the server running the Qlik Sense software, including unauthenticated remote code execution (RCE).
These issues were identified and responsibly reported to Qlik by Adam Crosser and Thomas Hendrickson of Praetorian.
Qlik has received reports that this vulnerability may be being used by malicious actors. Customers should confirm they have applied the necessary patches outlined in this bulletin. If there are additional questions, customers may log a case with Qlik Support.
Affected Software
All versions of Qlik Sense Enterprise for Windows prior to and including these releases are impacted:
- May 2023 Patch 3
- February 2023 Patch 7
- November 2022 Patch 10
- August 2022 Patch 12
Severity Rating
Using the CVSS V3.1 scoring system (https://nvd.nist.gov/vuln-metrics/cvss), Qlik rates one as high severity and one as critical.
Vulnerability Details
CVE-2023-41266 (QB-21220) Path traversal in Qlik Sense Enterprise for Windows
Severity: CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:L/A:N (8.2 High)
Due to improper validation of user supplied input, it is possible for an unauthenticated remote attacker to generate an anonymous session which allows them to perform HTTP requests to unauthorized endpoints.
CVE-2023-41265 (QB-21222) HTTP Tunneling vulnerability in Qlik Sense Enterprise for Windows
Severity: CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:C/C:H/I:H/A:N (9.6 Critical)
Due to improper validation of HTTP Headers a remote attacker is able to elevate their privilege by tunnelling HTTP requests, allowing them to execute HTTP requests on the backend server hosting the repository application.
Resolution
Recommendation
Customers should upgrade Qlik Sense Enterprise for Windows to a version containing fixes for these issues. Fixes are available for the following versions:
- August 2023 Initial Release
- May 2023 Patch 4
- February 2023 Patch 8
- November 2022 Patch 11
- August 2022 Patch 13
All Qlik software can be downloaded from our official Qlik Download page (customer login required).
-
Qlik Sense Enterprise on Windows: Cross Site Scripting (XSS) protection HTTP hea...
Content-Security-Policy (current) or X-XSS-Protection (outdated) headers are not set by default after installing Qlik Sense Enterprise on Windows. Wh... Show MoreContent-Security-Policy (current) or X-XSS-Protection (outdated) headers are not set by default after installing Qlik Sense Enterprise on Windows.
While potentially great for improving site security, Qlik has no authority over the environment Qlik Sense is deployed in. If the specific custom header or other headers are deemed necessary, they can be added to the virtual proxy from the Qlik Sense Enterprise Management panel. See Qlik Sense for Administrators: Virtual Proxies.
Related Content
Qlik Sense Enterprise on Windows: Securing and Hardening Server
-
Qlik Sense Enterprise on Windows: Information Leak in /api/about/v1/thirdParty
Security vulnerability scan report may refer to "System Information Leak" in the response from the About Service API end-point /api/about/v1/thirdPart... Show MoreSecurity vulnerability scan report may refer to "System Information Leak" in the response from the About Service API end-point /api/about/v1/thirdParty.
This API returns a list of third-party software that is installed in the product. Details include information about copyright, version, licensing, and legal notices.
The disclaimer text of some third-party components may include IP address references. These references come from the third-party provider's disclaimer or open-source license details. The IP address references do not refer to details from the installed environment.
For example, an internal IP address (10.x.x.x) is referred to in the disclaimer text for the Torch Cephes Math Library. This reference is part of the library's open-source license https://github.com/deepmind/torch-cephes/blob/master/LICENSE.txt.
Resolution
Third-party software details contain disclaimer text as required for the third-party software provider.
IP references in third-party software disclaimers can be considered false-positive test results.Qlik can not alter the third-party vendor disclaimers.
Related Content
Third Party: Get | Qlik Sense for developers Help
False PositiveEnvironment
-
Multi-Factor Authentication Not supported in QlikView
QlikView is an identity consumer, not an authentication provider. Based on this premise, QlikView cannot support Multi-Factor Authentication. If the i... Show MoreQlikView is an identity consumer, not an authentication provider. Based on this premise, QlikView cannot support Multi-Factor Authentication.
If the identity provider can pass the identity to QlikView in a manner it can consume after it's authenticated, then it would work. Still, it is a matter of sending an identity in a format QlikView can consume.
As such, MFA (Multi-Factor Authentication) is not supported.
Qlik Cloud and Qlik Sense Enterprise on Windows support Multi-Factor Authentication.
Related Content:
Qlik Cloud: Configuring Multi-Factor Authentication (MFA)
Qlik Sense Enterprise on Windows: Authentication solutions -
Change QlikView Services communication from Windows Group Authentication to Cert...
The QlikView Services communication can be changed from the traditional Windows Group Authentication to Certificate Trust. For basic instructions, s... Show More -
Qlik NPrinting and CVE-2022-37026 (Erlang version)
To address CVE-2022-37026, upgrade Qlik NPrinting to any version past May 2022 SR3. Environment Qlik NPrinting Internal Investigation ID(s) 000616... Show MoreTo address CVE-2022-37026, upgrade Qlik NPrinting to any version past May 2022 SR3.
Environment
Internal Investigation ID(s)
00061646
-
Question regarding Qlik Replicate and a Java SE Vulnerability
It was reported that Qlik Replicate May 2022 (2022.5.0.291) version reports a Java SE vulnerability: Plugin Output: Path : /opt/attun... Show MoreIt was reported that Qlik Replicate May 2022 (2022.5.0.291) version reports a Java SE vulnerability:
Plugin Output: Path : /opt/attunity/replicate/jvm/ Installed version : 11.0.14 Fixed version : Upgrade to version 11.0.16 or greater CVE-2022-21426,CVE-2022-21434,CVE-2022-21443,CVE-2022-21449,CVE-2022-21476,CVE-2022-21496 CVE-2022-21540,CVE-2022-21541,CVE-2022-21549,CVE-2022-25647,CVE-2022-34169
Environment
- Qlik Replicate version May 2022
- Linux
Resolution
Qlik Data Integration products use JVM version 11 for QEM/Replicate and also JVM version 8 for Compose.
There is no need to patch Qlik Replicate itself.
To address the security report, you can independently upgrade Java SE to 11.0.17 on the server Qlik Replicate is running on.
Internal Investigation ID(s)
7345
-
Are Qlik Replicate Instances non-PCI Compliant?
A security scan may report that Qlik Replicate instances are non-PCI compliant due to weak SSL ciphers on ports 443, 3389 and 3552. Out of these ports... Show MoreA security scan may report that Qlik Replicate instances are non-PCI compliant due to weak SSL ciphers on ports 443, 3389 and 3552.
Out of these ports, 443 and 3552 are used by Qlik. Port 3389 is RDP.
Environment
- Qlik Replicate
- Windows
Resolution
The security of Qlik products does not depend only on the Qlik software. It also relies on the security of the environment that, in this case, Qlik Replicate operates in. This means that the security of, for example, the operating system and the cryptographic protocols (such as TLS/SSL) has to be set up and configured to provide the security needed for Qlik Replicate.
Qlik cannot offer advice on how to configure Windows to disable certain ciphers which customer security guidelines forbid.
For information on how to mitigate these reports, please see: https://learn.microsoft.com/en-us/windows-server/security/tls/tls-registry-settings.
Lucky 13 and Sweet 32 are the versions which are not compliant for port 3552.
Luck-13 (https://crashtest-security.com/prevent-ssl-lucky13/) and Sweet-32 (https://crashtest-security.com/prevent-ssl-sweet32/) are not versions, nor are they ciphers that Replicate uses on port 3552. Those are old vulnerabilities (5Y+) that are either mitigated in the version of OpenSSL currently used in Qlik Replicate (with its cipher selection) or is otherwise impractical or irrelevant in the way Qlik Replicate works.