Unlock a world of possibilities! Login now and discover the exclusive benefits awaiting you.
Qlik Sense documentation and resources.
Recent Documents
-
Configuring AWS S3 Blob Storage in Qlik SaaS (Qlik Cloud Services, Qlik Sense Bu...
Objective:For this document, we will review how to setup a connection to an AWS S3 bucket using Qlik SaaS (Qlik Cloud Services and Qlik Sense Business... Show MoreObjective:
For this document, we will review how to setup a connection to an AWS S3 bucket using Qlik SaaS (Qlik Cloud Services and Qlik Sense Business).
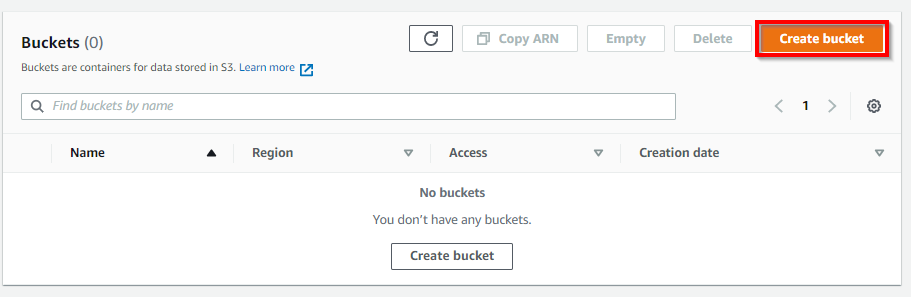
AWS S3 Setup:- Navigate to the S3 Service and create a bucket
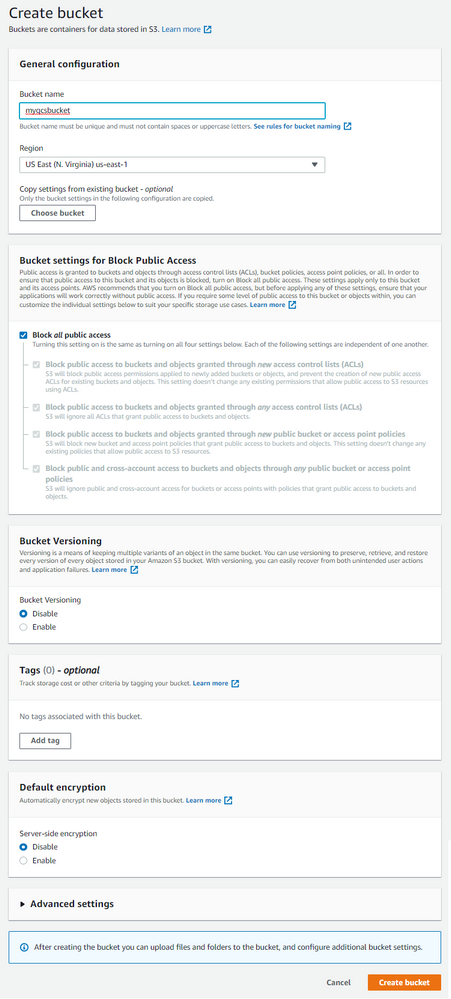
- Specify a name (which will need to be unique, globally), select the desired region.
- Note: It is highly recommended to leave the default Block all public access setting. Qlik SaaS does not require a public bucket for use and use of a public bucket is considered extremely risky from a data security perspective.
AWS IAM ConfigurationSince Qlik SaaS uses IAM user accounts to connect to S3, we will create an IAM user who will have full control over the S3 bucket. An optional configuration will be outlined later which will create an IAM user who has only read rights to the bucket. This shows the ability of Qlik SaaS to inherit granular IAM rights to buckets. For example, creation of read and read / write users who are scoped to departments is possible an encouraged in Qlik SaaS.
- Navigate to the IAM Service in the AWS Console
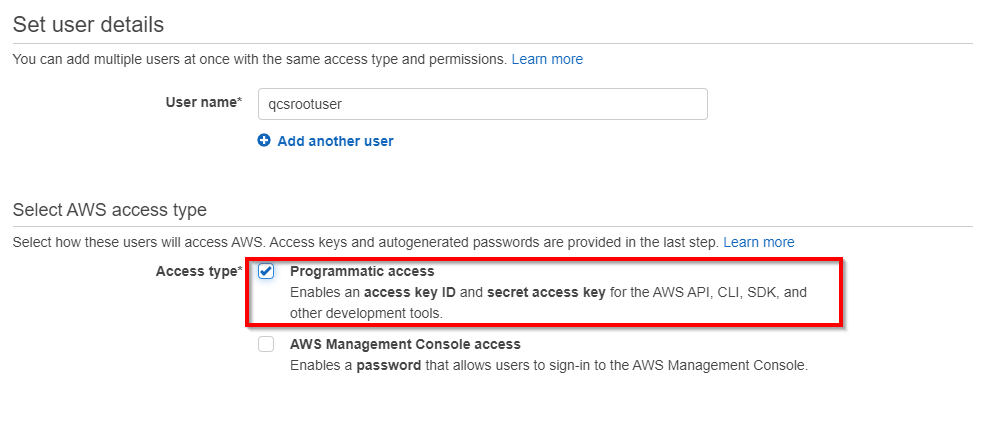
- Create a user. The Access Type should be set to Programmatic access so that the account has an access key and secret key.
- We will apply permissions at the bucket level, so continue through Permissions
- Tags are optional so configure if used in your AWS tenant
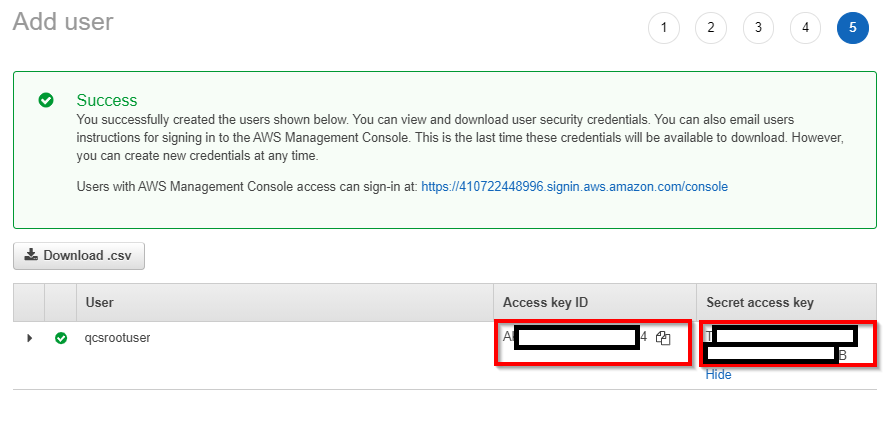
- Copy both the Access Key and Secret Key
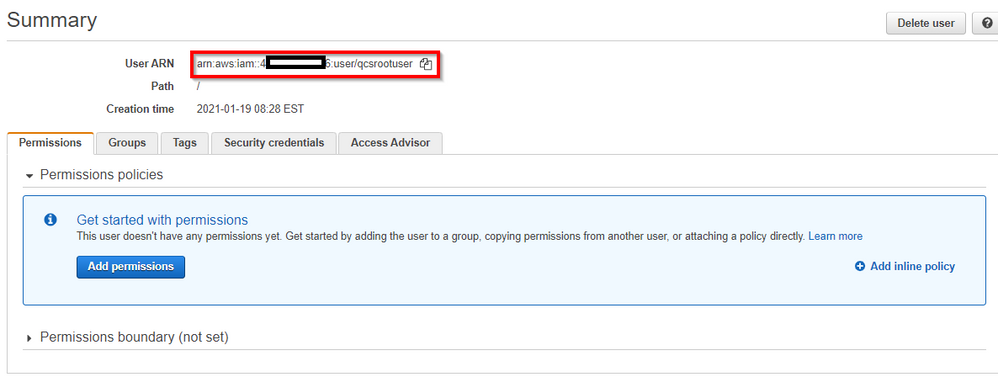
- Navigate to the newly created user’s record in IAM and copy the User ARN
AWS S3 Configuration
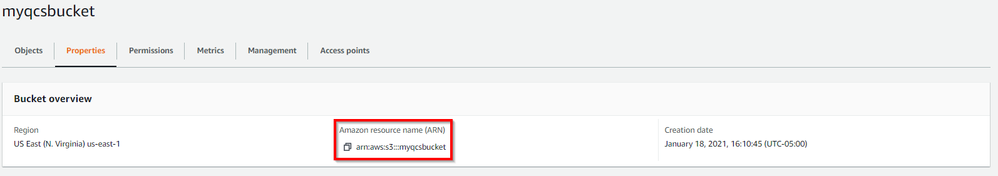
- Navigate to the Properties panel of the S3 bucket and copy the bucket's ARN
- Navigate to the S3 bucket’s Permissions configuration and edit the Bucket Policy. An example broad policy which permits full access to all files in the bucket can be adapted from this schema:
{ "Version": "2012-10-17", "Statement": [ { "Effect": "Allow", "Principal": { "AWS": [ "arn:aws:iam::<myIAMuser>" ] }, "Action": "s3:ListBucket", "Resource": "arn:aws:s3:::<myS3Bucket>" }, { "Effect": "Allow", "Principal": { "AWS": "arn:aws:iam::<myIAMuser>" }, "Action": [ "s3:GetObject", "s3:PutObject" ], "Resource": "arn:aws:s3:::<myS3Bucket>/*" } ] }Qlik SaaS Configuration
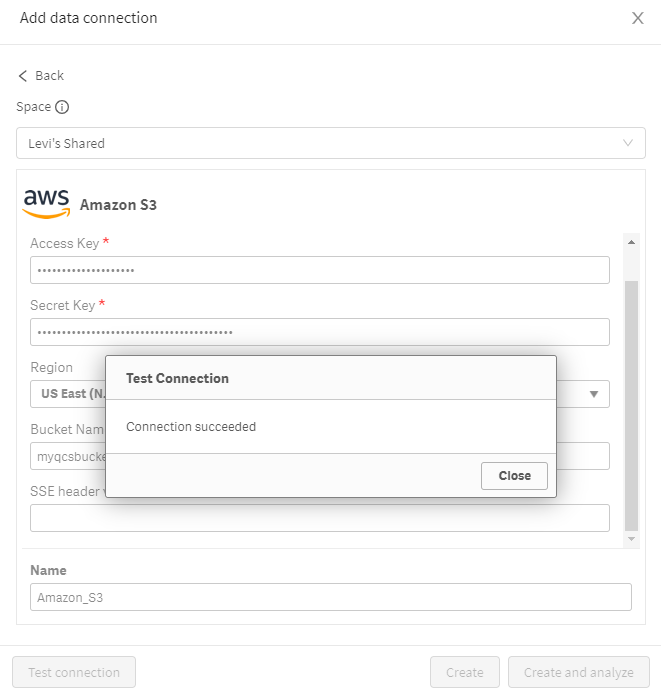
In Qlik SaaS, users can create data connections in two places: inside of a Qlik app or in the Hub. For this guide, we will use the Hub option.- Navigate to the desired space for the data connection, select the gear icon, and select Data sources
- Scroll to Data Connections and add a data connection
- Select Amazon S3
- Enter the Access Key and Secret key for the IAM user along with the appropriate bucket name and AWS region
Alternative Policy ConfigurationAs mentioned above, with AWS's Policy flexibility, we can create custom policies on the bucket which give a low level of granular control over which user(s) can do which actions on which files.
To provide two examples of this flexibility:
Option 1 - Read-Only vs. Read/Write Access
This policy provides for separation of read and read/write activities:
{ "Version": "2012-10-17", "Statement": [ { "Effect": "Allow", "Principal": { "AWS": [ "arn:aws:iam::<myReadUser>", "arn:aws:iam::<myReadWriteUser>" ] }, "Action": "s3:ListBucket", "Resource": "arn:aws:s3:::<myS3Bucket>" }, { "Effect": "Allow", "Principal": { "AWS": "arn:aws:iam::<myReadWriteUser>" }, "Action": [ "s3:GetObject", "s3:PutObject" ], "Resource": "arn:aws:s3:::<myS3Bucket>/*" }, { "Effect": "Allow", "Principal": { "AWS": "arn:aws:iam::<myReadUser>" }, "Action": "s3:GetObject", "Resource": "arn:aws:s3:::<myS3Bucket>/*" } ] }Option 2 - Root User vs. Read-Only Line of Business / Project / Department
This policy provides for a read-only user who is scoped to purely a specific "folder" for a department / project / line of business:
{ "Version": "2012-10-17", "Statement": [ { "Effect": "Allow", "Principal": { "AWS": [ "arn:aws:iam::<myReadOnlyDepartmentUser>", "arn:aws:iam::<myRootUser>" ] }, "Action": "s3:ListBucket", "Resource": "arn:aws:s3:::<myS3Bucket>" }, { "Effect": "Allow", "Principal": { "AWS": "arn:aws:iam::<myRootUser>" }, "Action": [ "s3:GetObject", "s3:PutObject" ], "Resource": "arn:aws:s3:::<myS3Bucket>/*" }, { "Effect": "Allow", "Principal": { "AWS": "arn:aws:iam::<myReadOnlyDepartmentUser>" }, "Action": "s3:GetObject", "Resource": "arn:aws:s3:::<myS3Bucket>/<myDepartmentFolder>/*" } ] } -
Qlik Sense Platform Concepts 2
Second list of words that appears during a standar customer installation.Please let me know if i went wrong with any concept.ConceptBrief DescriptionA... Show MoreSecond list of words that appears during a standar customer installation.
Please let me know if i went wrong with any concept.
Concept
Brief Description
ABAC
Attribute Based Access Control, also known as policy-based access control for IAM, defines an access control paradigm whereby access rights are granted to users through the use of policies which combine attributes together.
IAM
AWS Identity and Access Management (IAM) is a web service that helps you securely control access to AWS resources. Use IAM to control who is authenticated (logged in) and authorized (has permissions) to use resources.
Rugged software
For software to be considered as rugged, it must cope with all potential threats to the confidentiality, integrity, and availability of the information, and be robust when used in ways not anticipated.
“Rugged” describes software development organizations that have a culture of rapidly evolving their ability to create available, survivable, defensible, secure, and resilient software.NTLM
In a Windows network, NT (New Technology) LAN Manager (NTLM) is a suite of Microsoft security protocols intended to provide authentication, integrity, and confidentiality to users. NTLM is the successor to the authentication protocol in Microsoft LAN Manager (LANMAN), an older Microsoft product.
UPN
In Windows Active Directory, a User Principal Name (UPN) is the name of a system user in an email address format. A UPN (for example: john.doe@domain.com) consists of the user name (logon name), separator (the @ symbol), and domain name (UPN suffix).
Kerberos
Is a computer-network authentication protocol that works on the basis of tickets to allow nodes communicating over a non-secure network to prove their identity to one another in a secure manner.
STRIDE
Is a model of threats developed by Praerit Garg and Loren Kohnfelder at Microsoft[1] for identifying computer security threats.[2] It provides a mnemonic for security threats in six categories.[3]
The threats and Desired properties are :
Spoofing → Authenticity
Tampering → Integrity
Repudiation → Non-repudiability
Information disclosure → Confidentiality
Denial of Service → Availability
Elevation of Privilege → AuthorizationChecksums
Is a small-sized datum derived from a block of digital data for the purpose of detecting errors that may have been introduced during its transmission or storage. By themselves, checksums are often used to verify data integrity but are not relied upon to verify data authenticity.
PEM
Is an ASCII text format for public certificates. It is portable across platforms
JWT
JSON Web Token is an open standard for secure transmission of information between two parties as a JavaScript Object Notation (JSON) object. JWT is used for authentication and authorization. Because JWT enables single sign-on (SSO) , it minimizes the number of times a user has to log on to cloud applications and websites.
Certificates
Qlik Sense uses certificates to secure communication between components that are installed on different computers.A certificate is a data file that contains keys that are used to encrypt communication between a client and a server in a domain. Certificates also confirm that the domain is known by the organization that issued the certificate.
SAML
Security Assertion Markup Language. Is an open standard for exchanging authentication and authorization data between parties, in particular, between an identity provider and a service provider. SAML is an XML-based markup language for security assertions (statements that service providers use to make access-control decisions)
SPN
Service principal name, is a unique identifier of a service instance.
SPNs are used during authentication to associate a service instance with a service logon account. This allows a client application to request that a service authenticate an account even if the client does not have the account name. A SPN always includes the name of the host computer on which the service instance is running, so a service instance might register a SPN for each name or alias of its host.SSO
Single sign-on is a centralized session and user authentication service in which one set of login credentials can be used to access multiple applications.
log4net library
The Apache log4net library is a tool to help the programmer output log statements to a variety of output targets. log4net is a port of the excellent Apache log4j™ framework to the Microsoft® .NET runtime. We have kept the framework similar in spirit to the original log4j while taking advantage of new features in the .NET runtime.
Kubectl
The kubectl command line tool lets you control Kubernetes clusters.
Shared Persistence
This means that nodes share a single repository database and a network folder for the application files. You can either share the central node repository and application storage, or setup dedicated machines for repository and application storage.
TLS
Transport Layer Security (TLS) is the successor protocol to SSL. TLS is an improved version of SSL. It works in much the same way as the SSL, using encryption to protect the transfer of data and information. The two terms are often used interchangeably in the industry although SSL is still widely used.
UNC
Universal Naming Convention) A standard for identifying servers, printers and other resources in a network, which originated in the Unix community. A UNC path uses double slashes or backslashes to precede the name of the computer.
-
4 dynamic use cases for Input Forms | Qlik Sense Writeback capabilties
In today’s BI environment, there’s a growing need to take action directly where your data is, to bring everything together and close the analytics loo... Show MoreIn today’s BI environment, there’s a growing need to take action directly where your data is, to bring everything together and close the analytics loop!
Vizlib’s writeback capabilities enable you to transform your insights into data-driven action. You can capture user input and enter new data points directly into your published Qlik Sense apps.
Here are 4 ways your business can gain additional value from Vizlib Input Form.
1. Create surveys on the fly
Many industries need to create surveys on the fly. For instance, in retail, customer surveys are crucial for keeping in touch with customer needs.
Vizlib Input Form provides a safe way to capture survey information where the data is, and integrates with 3rd party software, like Survey Monkey or Google, to deliver additional value.
In the healthcare sector, users can safely capture crucial patient information directly into Qlik Sense, saving time and ensuring patient information remains confidential.
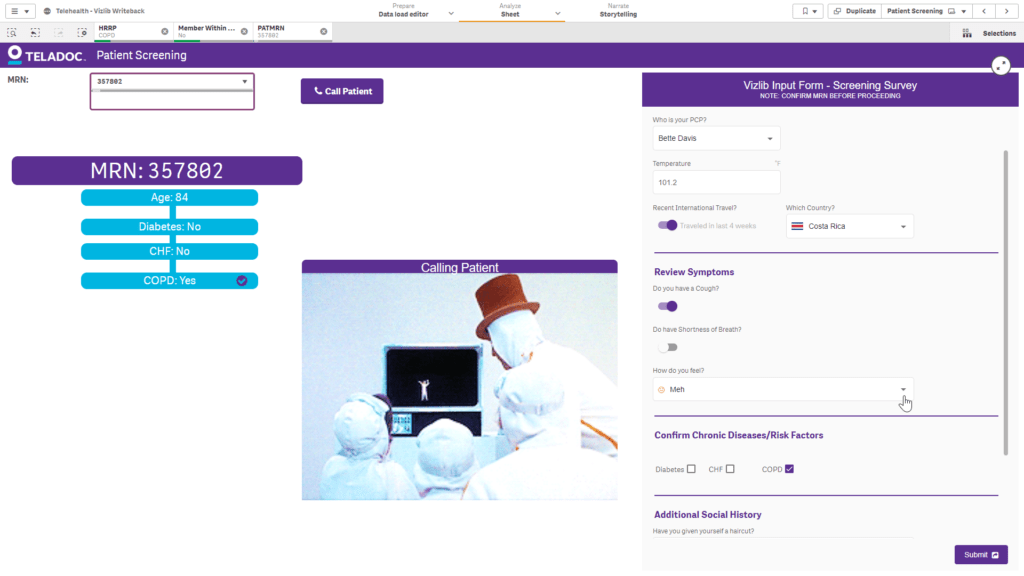 Vizlib Input Form: Telehealth patient screening survey
Vizlib Input Form: Telehealth patient screening survey2. Data-driven performance reviews
 Vizlib Input Form: Sales performance review
Vizlib Input Form: Sales performance reviewPerformance reviews should be based on data to provide an accurate picture of how every aspect of your business is performing. Yet, the review process often feels tedious.
With Vizlib Input Form, you can quickly and easily review your business KPIs. Dynamically populate your Vizlib Input Form with Qlik KPIs as you make selections, add comments, scores, and any other input type, then write the data to kick off a workflow.
This practical capability also integrates with other business platforms enabling you to write your data to any destination such as Slack, email, or a whole workflow, and get the right insights across immediately!
3. Improve access control management
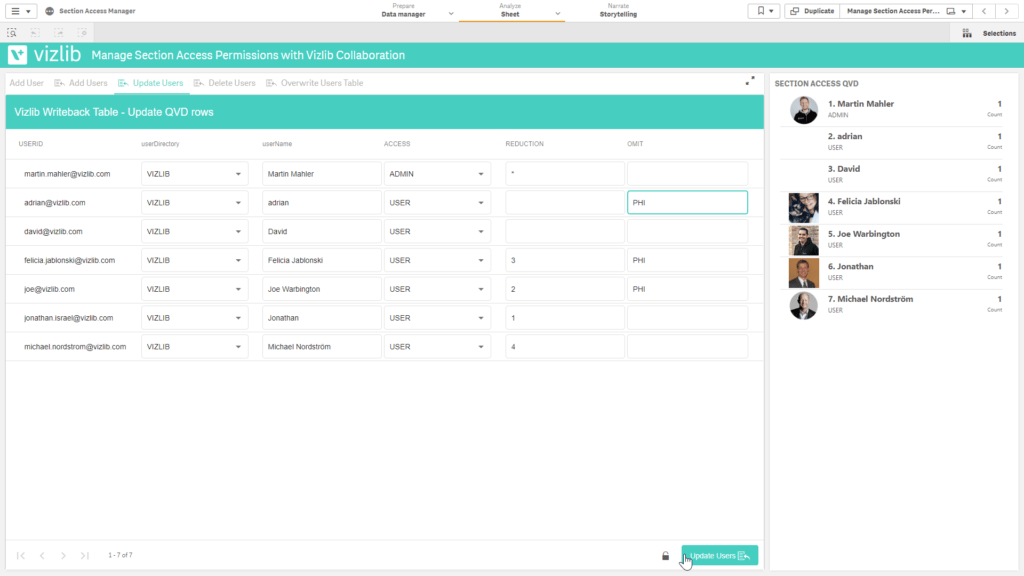
Vizlib Writeback Table and Vizlib Input Form: Improving access control management
Vizlib Input Form provides a user-friendly interface that empowers you to manage section access and other mapping files, such as master data management, without the help of a database administrator. It’s easy to add a new user with Vizlib Input Form or to delete users. Together with Vizlib Writeback Table, you can check what permission levels other team members have for improved access control management.
4. Easily change Qlik variables
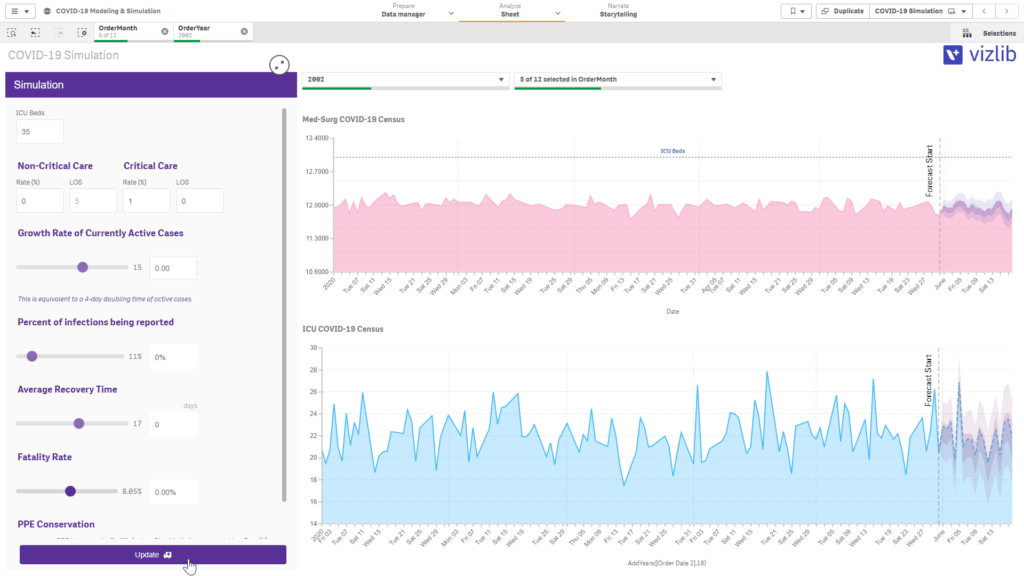
Vizlib Input Form: Updating and running COVID-19 simulations and predictions for a hospital system
Vizlib Input Form enables you to run simulations on the fly, explore what-if scenarios, show forecasting and enable rapid prototyping. In the healthcare sector, users can easily update the number of beds, length of stay, or current infection rate and forecast when they’re likely to see peaks and drops. It’s easy to tie into your particular business system.
Get a streamlined, safe and user-friendly input capability to kickstart your analytics process with Vizlib Input Form.
Learn more and try out Vizlib Input Form, Writeback Table, and Teamwork as part of Vizlib Collaboration for Qlik Sense: https://home.vizlib.com/vizlib-collaboration-for-qlik-sense/