Unlock a world of possibilities! Login now and discover the exclusive benefits awaiting you.
- Qlik Community
- :
- Support
- :
- Support
- :
- Knowledge
- :
- Support Articles
- :
- Qlik Sense Enterprise on Windows Mixed Content and...
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Qlik Sense Enterprise on Windows Mixed Content and CORS error for Access-Control-Allow-Origin, Mashup fails to load when deployed on web server
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Qlik Sense Enterprise on Windows Mixed Content and CORS error for Access-Control-Allow-Origin, Mashup fails to load when deployed on web server
Mar 25, 2026 10:09:54 AM
Jan 8, 2019 10:21:10 AM
A Mixed Content error and CORS errors are displayed in a Qlik Sense Enterprise on Windows Environment running HTTPS, and a Web server hosting a mashup on HTTP.
Qlik Sense Mashups may fail to render when deployed to a web server.
Example setup:
- Webapp server is running HTTP (e.g. in development)
- Qlik is running HTTPS only.
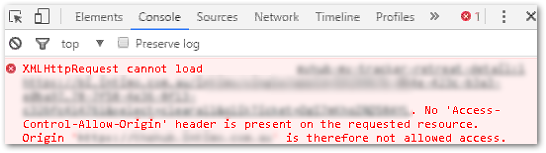
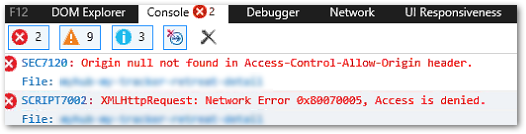
Example error messages:
Access to XMLHttpRequest at [] from origin '[]' has been blocked by CORS policy: The 'Access-Control-Allow-Origin' header has a value '[]' that is not equal to the supplied origin.
Origin null not found in Access-Control-Allow-Origin header.
XMLHttpRequest cannot load. No 'Access-Control-Allow-Origin' header is present on the requested resource.
Resolution
Avoid mixed content
The first solution is to avoid mixed content (HTTP and HTTPS). If this cannot be avoided, configure the required additional response header for CORS protection.
Enable CORS protection
Before configuring CORS protection, verify that the host is included in the Host allow list. For details on how this is configured, see How to configure the WebSocket origin allow list and best practices.
Example: A mashup is hosted on http://localhost:8080, and Qlik Sense is hosted on https://my-sense-server. Including "localhost" in the allow list is not sufficient; include explicitly both the protocol and port in this case (* will not include the port):
If you have multiple hostnames, include all in the allow list.
To configure the additional response header for CORS protection:
- Open the Qlik Sense Management Console
- Navigate to Virtual proxies
- Select the Virtual proxy in use for the hub
- Expand the Advanced properties
- Configure the Additional response headers by adding the following:
Access-Control-Allow-Credentials: true
Access-Control-Expose-Headers: qlik-csrf-token
Example:
If the allow list and CORS protection have been configured correctly in Qlik Sense, but the issue continues, the root cause may be your web portal or web page host's configuration. Contact the web service provider or web server administrator for further troubleshooting and configuration.
Environment:
Qlik Sense Enterprise on Windows
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Is `Access-Control-Allow-Origin` still required in Qlik Sense May 2025? I found it to be set automatically if I access a mashup from https://localhost:3000, the header is https://localhost:3000, if I access it from https://localhost:3001, it is https://localhost:3000. If I access it from https://hostname/extensions/myextension/index.html , the header is not there (as the origin is the same as the engine api requests, the header is not necessary).
If I set the header to "https://foobar" or "https;//localhost:3000", the behavior does not change at all, it still sets the header for port 3000 and 3001.
It seems it is set automatically and setting it in the virtual proxy has no effect at all.
(There is no HTTP proxy in between that could add the header.)
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Typo. Corection: if I access it from https://localhost:3001 , it is https://localhost:3001
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hello @christopherkramer
I checked with one of our subject matter experts on this:
It's based on the host allow list; no need to input ports. Localhost and actual servername (not external DNS names) are automatically considered trusted, so you only need to add external DNS names or mashup server names to the allowlist.