Unlock a world of possibilities! Login now and discover the exclusive benefits awaiting you.
- Qlik Community
- :
- All Forums
- :
- Mobile Discussions
- :
- Qlik Sense® integration with MobileIron
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Qlik Sense® integration with MobileIron
This article is a comprehensive guide on the current integration of Qlik Sense with MobileIron as at 31 March 2018.
![]()
Recommendation:
Qlik recommends that customers prove the operation of Safari and/or Web@Work Browser with their Enterprise Mobile Management (EMM) Infrastructure, and familiarise with the deployment and configuration of Qlik Sense Mobile without per-App VPN connectivity (AppConfig "mdm" property, QMC Security Rules). Ensure that MobileIron is iOS v11-ready1 and using MobileIron Sentry v9 (or greater) to provide per-App VPN connectivity from Browsers. The same per-App VPN connectivity is planned to be supported for Qlik Sense Mobile.
Qlik Sense requires that clients and intermediate infrastructure support websocket connectivity that is used between the Qlik Visualizations and the Qlik Sense Proxy service for retrieval of Associative datasets. Websockets are part of the HTML5 standard, but many proxy servers fail to support it; iOS v11 has resolved previous issues with routing websocket traffic via any per-App VPN. Remaining connectivity problems are now due to configuration/limitations of EMM and other network infrastructure. The following is a comprehensive guide on the current integration of Qlik Sense with MobileIron.
MobileIron:
MobileIron describe1 several minimum requirements for their support of iOS v11, particularly:
- MobileIron Go 2 v3.0
- MobileIron Tunnel 3 v2.2.6
- Web@Work Browser 4 v2.1
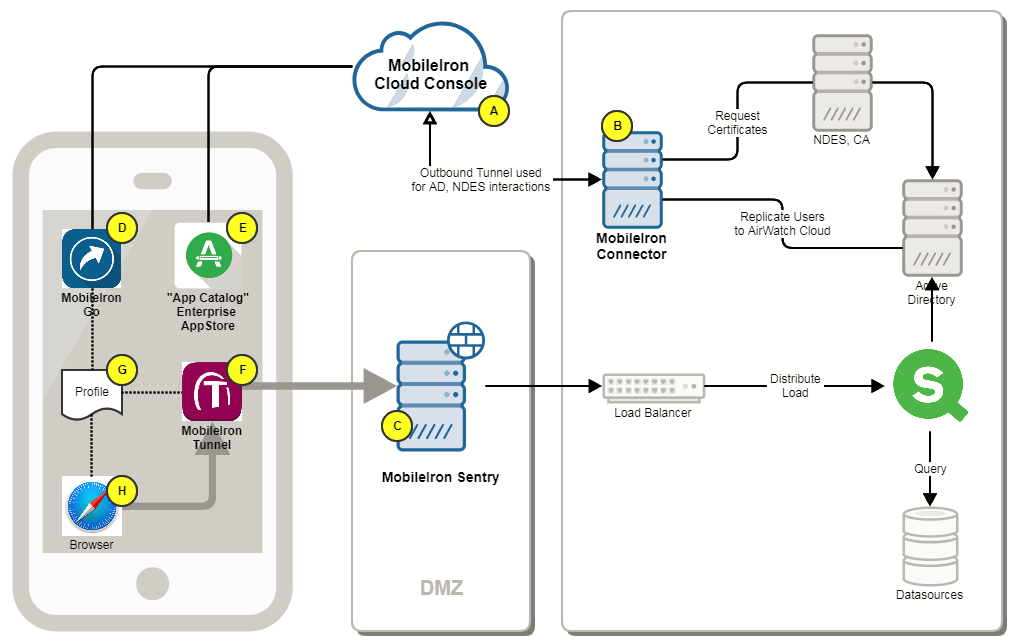
(A) Customer can utilise the SaaS MobileIron Cloud, or implement the MobileIron Core onPremise
(B) MobileIron Connector 5 is installed behind the Firewalls, providing replication services from Active Directory to the SaaS Console. The software can be downloaded from the MobileIron Console.
(C) The MobileIron Sentry is deployed in DMZ as the VPN gateway to private resources. The software can be downloaded from the MobileIron Console or instantiated from an Amazon EC2 AMI.
(D) The mobile user performs Self-Service enrolment by installing MobileIron Go from iTunes then browsing to https://mobileiron.com/go MobileIron Go is the agent which MobileIron uses to manage the device.
(E) Successful Enrolment will add the Enterprise AppStore App Catalog, which is where Managed Applications can be installed from instead of using the Apple App Store.
(F) The MobileIron Tunnel VPN client may be automatically installed immediately after successful enrollment, or can be downloaded from the App Catalog. This will use an SSL Client Certificate (G) to perform Device Authentication to the MobileIron Sentry and create a Tunnel through which traffic from Managed Applications can reach private resources such as Qlik Sense.
(G) Configuration details are delivered by MobileIron Go to iOS as "profiles". These are visible in the iOS Settings application. A profile may include Rules for which Browser uses the VPN to access which URLs, but also other features such as WebClips (URL Shortcuts), Email Configuration and SSL Certificates.
(H) Safari or a Managed Application (eg Qlik Sense Mobile or MobileIron's Web@Work Browser installed from the App Catalog) will use a Profile (G) to determine whether it should have an exclusive and private (per App VPN) conversation with the MobileIron Tunnel (F) VPN client to access a Qlik Sense URL.
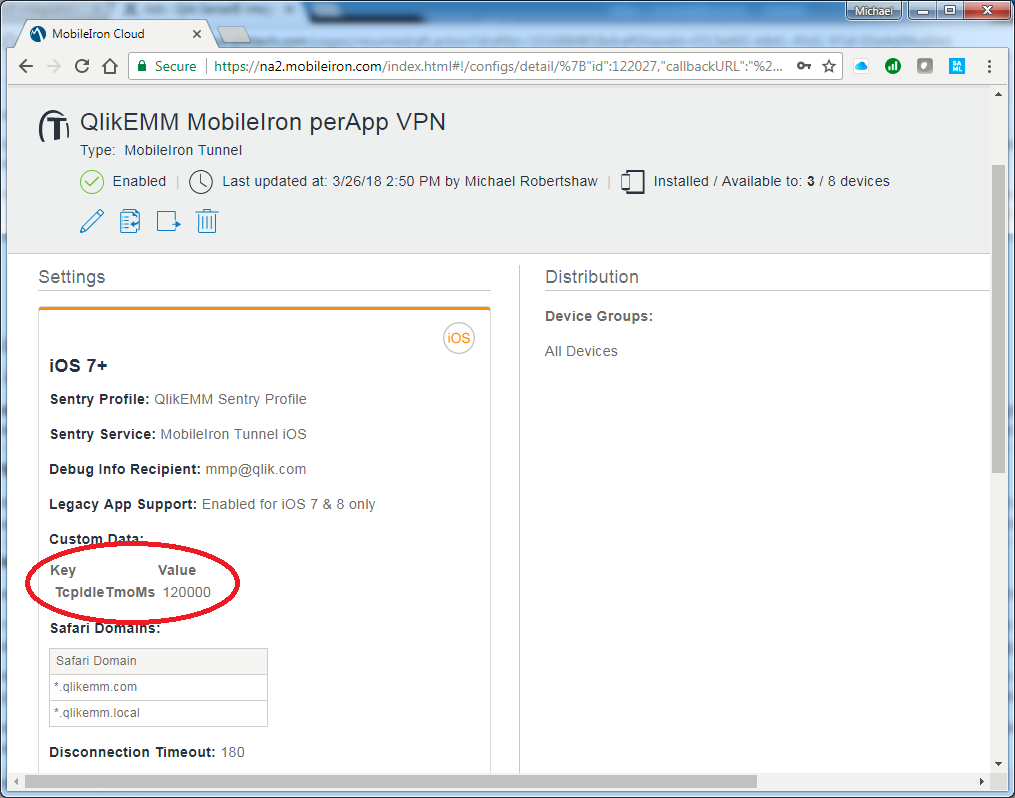
Browser Users will be disconnected from Qlik Sense by MobileIron if they are inactive, and will be shown a "Connection Lost" error message. They can recover their session by simply refreshig the browser but their Current Selections would be lost. This global timeout is configurable as a property of the MobileIron Tunnel configuration item, and defaults to 60000 milliseconds (1 minute). It is necessary to add a Custom Data KeyValuePair to the MobileIron Tunnel Configuration, as per MobileIron documentation,6 to assign TcpIdleTmoMs a reasonable value such as 300000 milliseconds (5 minutes). Note that this is different from the Disconnection Timeout property that is shown in the configuration dialog!
Testing configuration:
A diagnostic webpage can be downloaded from branch.qlik.com 7 and should be deployed into the Qlik Sense Content Library via the QMC. Access this deployed content using mobile browsers to determine if websockets are supported by the browser, VPN and other network infrastructure. Load Balancers between the Qlik Sense Proxy instances may require additional configuration 8 to support websocket traffic.
Qlik Sense Mobile (iOS app):
Qlik Sense Mobile provides an online alternative to a browser, and implements our Associative Engine on iOS to also provide offline data analysis on Qlik documents that have been synchronised to the device.
Qlik Sense Mobile is currently supported for deployment and configuration by MobileIron, but not 9 yet (31 March 2018) for operation together with the MobileIron Tunnel per-App VPN.
Deployment
Qlik Sense Mobile is currently available from the Apple AppStore 10 and can be added to the MobileIron App Catalog as a Managed Application.
Configuration
When installed from the MobileIron App Catalog, MobileIron can supply configuration details too. A single text variable "mdm" can be specified, as documented on at help.qlik.com 11, and contains a JSON array that delivers a collection of Qlik Sense Hub URLs to Qlik Sense Mobile rather than requiring that users browse to the Qlik Sense Hub and download a "Client Authentication Link".
| mdm |
|---|
{ "Accounts" : [ {"name": "United Kingdom", "url": "https://sense.uk.example.com"}, {"name": "Brazil", "url": "https://sense.br.example.com"} ] } |
When supplied to Qlik Sense Mobile from MobileIron Core, an XML representation of AppConfig may be required, as follows:
| AppConfig |
|---|
<?xml version="1.0" encoding="UTF-8"?> <!DOCTYPE plist PUBLIC "-//Apple//DTD PLIST 1.0//EN" "http://www.apple.com/DTDs/PropertyList-1.0.dtd"> <plist version="1.0"> <dict> <key>mdm</key> <string> { "Accounts": [ {"name": "United Kingdom", "url": "https://sense.uk.example.com"}, {"name": "Brazil", "url": "https://sense.br.example.com"} ] } </string> </dict> </plist> |
Per App VPN
It is clear that per-App VPN connectivity is required for Remote/Home office users who want to interact with Qlik Sense online or to sync documents to their device for offline use. As of 31 March 2018, Qlik has determined that Qlik Sense Mobile operates as intended with Device-level VPN products, but not with MobileIron Tunnel per-App VPN.
MobileIron has confirmed (16 April 2018) to Qlik that the MobileIron Tunnel VPN client improperly intercepts TCP traffic within the App, and does not route traffic as Qlik intends. This is due to the way that iOS delivers ALL app traffic to the VPN client, and the VPN client is forwarding all traffic to the MobileIron Sentry. The MobleIron Sentry contains a configurable Advanced Traffic Control feature but the routing of traffic needs to be adjusted on the iOS client before potentially being delivered to the MobileIron Sentry. MobileIron have raised a case with Apple (Apple RADAR ID: 33553614) seeking adjustment to this behaviour in iOS.
Without an enhancement to the MobileIron Tunnel VPN client, users see only a blank screen when activating Qlik Sense Mobile in conjunction with the MobileIron Tunnel per-App VPN.
Mutual customers affected by this issue are advised to open Support Calls with both MobileIron and Apple. With sufficient customer pressure, MobileIron should modify their VPN client to route localhost (localhost, IPv6 ::1, IPv4 127.0.0.1) traffic back to the device instead of passing it from the device through to the MobileIron Sentry.
The MobileIron Tunnel per-App VPN does appear to work satisfactorily with mobile browsers as described in an earler section.
Qlik Sense
Within the Qlik Sense Management Console you must configure Security Rules to permit Offline use of Qlik Sense documents. An example is provided at help.qlik.com 12
Only Users with a User Access Token can use Qlik Sense Mobile offline. Login tokens may not be used to synchronise content for Offline use.
Links:
MobileIron Guidance on iOS 11 Compatibility: https://community.mobileiron.com/docs/DOC-6671
MobileIron Guidance on iOS 12 Compatibility: https://community.mobileiron.com/docs/DOC-7938MobileIron Go: https://itunes.apple.com/us/app/mobileiron-go/id672836503?mt=8
MobileIron Go 3.0.0 for iOS Release Notes: https://community.mobileiron.com/docs/DOC-6923
- MobileIron Tunnel: https://itunes.apple.com/us/app/mobileiron-tunnel/id1150035878?mt=8
MobileIron Tunnel 2.3.1 for iOS Release Notes: https://community.mobileiron.com/docs/DOC-7230 - Web@Work Browser: https://itunes.apple.com/us/app/mobileiron-web-work/id596170970?mt=8
MobileIron Web@Work 2.3.0 for iOS Release Notes: https://community.mobileiron.com/docs/DOC-7581 - MobileIron Cloud Connector: http://mi.extendedhelp.mobileiron.com/50/all/en/desktop/Connector.htm
- MobileIron Tunnel for iOS Guide for Administrators: https://community.mobileiron.com/docs/DOC-6414 pp13
- Websocket Diagnostic Page: http://branch.qlik.com/#!/project/56728f52d1e497241ae69865
- BIG-IP support for the WebSocket protocol: https://support.f5.com/csp/article/K14754
Citrix Netscaler: see bottom of https://docs.citrix.com/en-us/netscaler/11/system/http-configurations.html - Release Notes available from Qlik Download Site: https://da3hntz84uekx.cloudfront.net/QlikSense/12.52/0/QlikSenseMobile_February2018_ReleaseNotes.pdf particularly note at bottom of page 8.
- Qlik Sense Mobile: https://itunes.apple.com/us/app/qlik-sense-mobile/id1217049362?mt=8
- AppConfig: https://help.qlik.com/en-US/sense/February2018/Subsystems/PlanningQlikSenseDeployments/Content/Deplo...
- Security Rule for allowing Offline access: https://help.qlik.com/en-US/sense/February2018/Subsystems/ManagementConsole/Content/offline-access-t...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Michael,
Very informative, thanks for clarifying this. We are struggling for a while now trying to get the iOS app to work with Mobile Iron per-app VPN, but after reading your article I think we can stop our efforts.
Do you have any information regarding a timeline when the iOS app will support per-app VPN with Mobile Iron?
Thanks,
Steven
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Active work-in-progress investigation between Qlik R&D and MobileIron.
Qlik Sense Mobile contains basically three components, comparable to Qlik Sense Enterprise: a Browser, a Webserver, and the Qlik Sense Engine. Localhost traffic between these components is being incorrectly intercepted by the VPN client, when only connections to a remote Qlik Sense Hub should be routed towards the MobileIron Sentry.
Resolution may be a configuration item in MobileIron (the Advanced Traffic Rules section of the MobileIron Sentry appears promising, and comparable to a similar feature in AirWatch) but it currently appears that an enhancement to the MobileIron Tunnel client will be required.
We don't yet have any ETA for a resolution to this problem.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Michael,
I noticed you updated this document last week, but I can't find any new information regarding the (lack of) support for Mobile Iron per-app vpn. Do you have an estimated ETA for a resolution?
Thanks,
Steven
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We have no update on this situation yet.
When any VPN is active on iOS, Apple sends ALL network traffic to the VPN client app. The VPN client should then decide where to route the traffic, and the MobileIron Tunnel sends ALL traffic to the MobileIron Sentry including localhost traffic that Qlik Sense Mobile expects to remain on the device. Most other VPN products have client-side configurable routing rules but MobileIron Tunnel does not.
Qlik believes that MobileIron should enhance their VPN product. MobileIron appear to believe that Apple is responsible for improperly routing localhost traffic to their VPN. We currently (June 2018) have no expected resolution to this impasse, but mutual customers are advised to raise a Support Call to MobileIron and escalate it to their MobileIron Account Manager. When there is sufficient customer pain then MobileIron will prioritise an enhancement to their VPN client.
In the meantime, MobileIron customers can use a Browser together with MobileIron Tunnel to access Qlik Sense from iOS devices but are unable to use Qlik Sense Mobile together with MobileIron Tunnel.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Michael,
Can you share details about the enhancements (or workarounds) that were made in Qlik and in AirWatch that made is possible to use the per-app-VPN solution of AirWatch together with the Mobile app from Qlik.
I'm asking this because as a Qlik partner I'm helping a customer who is using Qlik Sense and MobileIron. MobileIron has told the customer that they now admit their VPN client improperly intercepts TCP traffic within the App. They are now actively looking for possible workarounds to solve this issue, but at the same time they are asking us to help them with this task.
Thanks,
Steven
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Within an AirWatch environment it is possible to configure client-side routing rules which are necessary to support Qlik Sense Mobile. These are documented at https://help.qlik.com/en-US/sense/September2018/Subsystems/PlanningQlikSenseDeployments/Content/Sens... and within this Mobile Community area. No further customisation, configuration or enhancement to Qlik Sense Mobile (QSM) is necessary for it to operate together with VMware Workspace ONE (formerly AirWatch).
At the moment (Sept 2018) we believe that MobileIron should enhance their VPN client. Alternative VPNs such as PulseSecure may be managed by MobileIron and may work as Qlik expects but have not yet been validated by Qlik. As many enterprise customers now also use Office365 they may also have access to the Azure AD Application Proxy which provides access to on-premise websites such as Qlik Sense Enterprise.
Today mutual Qlik/MobileIron customers can successfully use Browsers to interact with Qlik Sense via the MobileIron Tunnel, but any deployment of Qlik Sense Mobile (QSM) via MobileIron must be configured to NOT use MobileIron Tunnel. QSM users could access Qlik Sense Enterprise and download content from within their office network for use in AirPlane Mode but cannot currently interact with Qlik Sense Enterprise from QSM via the MobileIron Tunnel PerApp VPN.
Additionally, I understand that MobileIron is available at both Basic and Premium licence types. Basic (perhaps incorrect terminology) enables "AppConnect" features of the MobileIron Sentry VPN Service that may provide connectivity to on-premise resources but this does not support websockets and is thus not expected to support connectivity to Qlik Sense Enterprise. The higher Premium licence of MobileIron enables the MobileIron Tunnel perApp VPN capability but (as above) current routing limitations in the VPN Client enable only browsers and not Qlik Sense Mobile as a managed app.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Michael,
For the integration with MobileIron it would really help if the Qlik Sense Mobile app was AppConnect-enabled. MobileIron can make public apps AppConnect-enabled with their AppConnect SDK. AppConnect-enabled apps reside and run within a passcode of fingerprint protected secure container This provided an extra security layer on top of the standard passcode protection on the iOS device. MobileIron has done this before for other apps, for instance with the IBM Connections app.
For more information about MobileIron AppConnect, follow this link:
http://info.mobileiron.com/rs/mobileiron/images/appconnect_faq.pdf
Is this something you can discuss within Qlik?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Michael,
Thank you for this great post.
Do you know if per-App VPN connectivity is now supported for Qlik Sense Mobile?
Thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Latest situation is documented at https://community.qlik.com/t5/Technology-Partners-Ecosystem/MobileIron-and-Qlik-Sense/ta-p/1528960
Pretty good news for those who want to use Web@Work or Qlik Sense Mobile with MobileIron Tunnel!!