Unlock a world of possibilities! Login now and discover the exclusive benefits awaiting you.
- Qlik Community
- :
- All Forums
- :
- Deployment & Management
- :
- shared selection between 2 devises
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
shared selection between 2 devises
Im using he same app on my ipad and laptop in same time, bu when i make a selection in ipad , it come on my laptop olso ,
How i can remove this shared selection between ipad and laptop ?
Thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Its a built in feature as the selections are stored in the session of your logged in user.
You'd have to log in as someone else.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Riadh,
This is default (and marketed) behavior. But if you need to go this route then you can enable Extended security environment on the Virtual Proxy (QMC > Virtual Proxies > Select Virtual proxy in use > Advanced), like below:
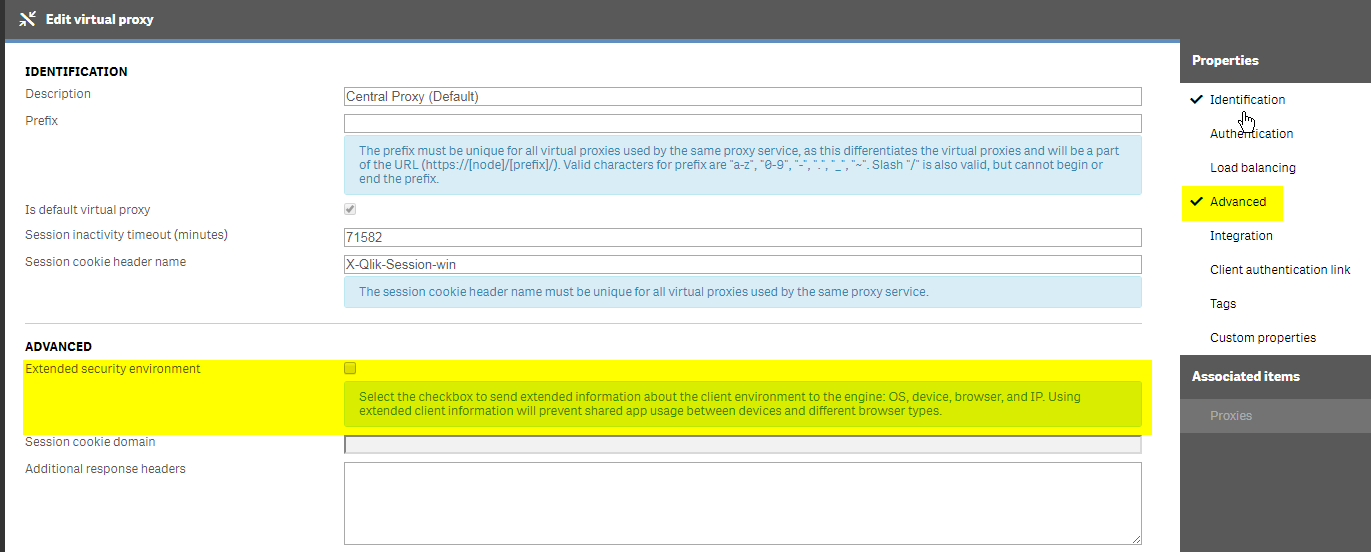
Keep in mind that this is a setting which is going to be set per virtual proxy and will apply to all sessions on this virtual proxy.
Hope this helps.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Levi,
Do you know whether this "Extended Security Environment" option helps to prevent concurrent access from multiple devices and browsers? I have enabled this and managed to get a message that inform user has no access when accessing from a different device/browser however this does not happen all the time and not very consistent. I have been advised by support to use security rule instead but do not know how. Do you have any idea?
Thanks.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Extended Security Environment does not disable concurrent logons. It simply disables the session sharing.
There is no mechanism that I am aware of inside of Qlik products to prevent concurrency. At its core, Qlik does not do authentication. We rely on authentication methods present inside of organizations (AD, IdPs in the case of SAML, etc).