Unlock a world of possibilities! Login now and discover the exclusive benefits awaiting you.
- Qlik Community
- :
- Support
- :
- Support
- :
- Knowledge
- :
- Support Articles
- :
- CVE_2021_44228 - Handling the log4j lookups critic...
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
CVE_2021_44228 - Handling the log4j lookups critical vulnerability for Qlik GeoAnalytics
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
CVE_2021_44228 - Handling the log4j lookups critical vulnerability for Qlik GeoAnalytics
Jan 27, 2022 4:13:15 AM
Dec 13, 2021 3:33:26 PM
Qlik GeoAnalytics Server and the Qlik GeoAnalytics Connector in combination with GeoAnalytics Plus are both affected by the log4j vulnerability.
Patches are available. See Vulnerability Testing - Apache Log4j, reference CVE-2021-44228 (also referred to as Log4Shell) for your release of Qlik GeoAnalytics and the relevant patch.
Upgrade at the earliest.
Mitigation steps are provided below should not upgrade be possible at this time.
The Standard GeoAnalytics Connector for Qlikview and QlikSense (bundled) without GeoAnalytics Plus are not affected by it, they don't use Java.
Environment:
Resolution for GeoAnalytics Server:
- Start the Configure Service application from the start menu.
- Set the Java options ‐Dlog4j2.formatMsgNoLookups=true inside the Service Properties under the Java tab.
- Restart all GeoAnalytics Services.
Resolution for GeoAnalytics Plus Connector:
- Open C:\Program Files\Common Files\Qlik\Custom Data\QvIdevioConnector\IdevioGeoAnalyticsConnector.exe.config
- Locate the following line (located in appSettings)
<add key="javaArgs" value=""/> - Change the line to:
<add key="javaArgs" value="-Dlog4j2.formatMsgNoLookups=true"/>
This applies only to GeoAnalytics Plus Connector Version May 2021 and higher.
Versions prior to February 2020 uses Log4j v1, which is not vulnerable to this exploit. To prevent any other possible vulnerabilities, we recommend upgrading to a newer version (higher than May 2021) of GeoAnalytics Plus and then applying the mitigation.
Alternatively, you can manually replace the Log4j library files with newer versions:
- Download the binaries of the latest release of Log4j2 (2.17.1 as of this moment): https://logging.apache.org/log4j/2.x/download.html
- Extract the files
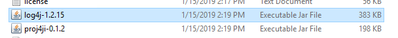
- Go to C:\Program Files\Common Files\Qlik\Custom Data\QvIdevioConnector\lib
- For all JAR files starting with "lib4j-"
- Copy the corresponding 2.17.1 JAR file to the lib folder
- Delete the old version of that JAR
For more information on the Log4j vulnerability, please visit the Support Updates Blog post.
As a short update we released:
- GeoAnalytics Server - 4.32.5 - (November 2021 SR3) - 2.17.1
- GeoAnalytics Server - 4.19.2 - 4.27.4 (February 2020 SR2 - May 2021 SR2) - 2.17.1
- GeoAnalytics Plus - 5.31.3 ( November 2021 SR3) - 2.17.1
- GeoAnalytics Plus - 5.29.5-5.30.2 (May 2021 SR3 - August 2021 SR2) - 2.17.1
- GeoAnalytics Plus - 5.27.6-5.28.3 (November 2020 SR2-February 2021 SR2) - 2.17.1
- GeoAnalytics Plus - 5.26.6 (September 2020 SR3) - 2.17.1
- GeoAnalytics Server - 4.32.4 - (November 2021 SR2) - 2.17.0
- GeoAnalytics Server - 4.32.3 - (November 2021 SR1) - 2.16.0
- GeoAnalytics Server - 4.19.1 - 4.27.3(February 2020 SR1 - May 2021 SR1) - 2.16.0
- GeoAnalytics Plus - 5.31.2 ( November 2021 SR2) - 2.17.0
- GeoAnalytics Plus - 5.31.1 ( November 2021 SR1) - 2.16.0
- GeoAnalytics Plus - 5.29.4-5.30.1 (May 2021 SR2 - August 2021 SR1) - 2.16.0
- GeoAnalytics Plus - 5.27.5-5.28.2 (November 2020 SR1-February 2021 SR1) - 2.16.0
- GeoAnalytics Plus - 5.26.5 (September 2020 SR2) - 2.16.0
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Does either or both of these fixes require outage at any point, i.e. service restarts?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
We are running Geo Analytics Server November 2018.
Does this change apply. Any info on whats supported and whats not?
Thanks,
Aadil
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Can we still expect a patch?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
@hermandup_anz:
The GA Server fix requires a restart of its service in order to apply.
The GA Plus fix similarly requires a restart if it is running. It will keep running in the background for a while after being used so you can open the process explorer and look for a matching Java process and kill that.
@aadil_madarveet:
GA Server Nov 2018 doesn't use Log4j 2 (we switched to ), it is using Log4j 1 so it is not vulnerable to this specific bug.
It is however quite outdated and might have other vulnerabilities in its dependencies so I would really recommend updating anyway.
@JohannaR:
We will focus on getting patches out for the latest versions first, and then go backwards (mainly since the earlier versions will need a bunch of build related changes backported which will require some work).
The first patches should be out by tomorrow at least.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Do you know from which version of GeoAnalytics the switch to Log4j 2 was made?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
@jfkinspariwe switched to Log4j2 in the February 2020 release of both GeoAnalytics Server and GeoAnalytics Plus.
I see that I forgot to add that to the post above.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hello
If there is no
<add key="javaArgs" value=""/>
line in config file , it need to be added ? If yes to which section ?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
@janyf which version are you using? it would come in the appsettings section between <appsettings> and </appsettings>
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
@janyf:
The option only works on GeoAnalytics Plus from the May 2021 version and onwards. I will ask the support team to update the page.
The recommended solution would be to upgrade to a newer version of GeoAnalytics Plus and then apply the mitigation.
You could also manually replace the Log4j library files with newer versions:
- Download the binaries of the latest release of Log4j2 (2.16 as of this moment): https://logging.apache.org/log4j/2.x/download.html and extract somewhere
- Go to C:\Program Files\Common Files\Qlik\Custom Data\QvIdevioConnector\lib
- For all JAR files starting with "lib4j-"
- Copy the corresponding 2.16 JAR file to the lib folder
- Delete the old version of that JAR
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
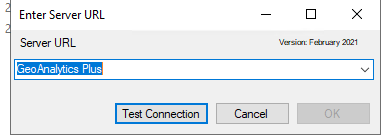
@KallePersson it is slightly confusing
This is library
but this is version when i run the connector :
so it is possible we are not affected somehow (as there is still old lib)
brgds