Unlock a world of possibilities! Login now and discover the exclusive benefits awaiting you.
Recent Documents
-
Qlik Sense Enterprise on Windows and Security Vulnerability CVE-2023-26136 (toug...
Is Qlik Sense Enterprise on Windows affected by the security vulnerability CVE-2023-26136 (nvd.nist.gov)? CVE-2023-26136 is a vulnerability detected i... Show MoreIs Qlik Sense Enterprise on Windows affected by the security vulnerability CVE-2023-26136 (nvd.nist.gov)?
CVE-2023-26136 is a vulnerability detected in Node.js, a third-party component used by Qlik Sense Enterprise on Windows. Security scans may flag the vulnerability in a Qlik Sense Enterprise on Windows environment.
While Qlik was not directly impacted, the affected third-party component has been updated across supported versions.
Qlik Sense versions up to the following would be flagged by security scans:
- Qlik Sense Enterprise on Windows May 2024 patch 23
- Qlik Sense Enterprise on Windows November 2024 patch 17
- Qlik Sense Enterprise on Windows May 2025 patch 5
Resolution
Upgrade to any of the following (or later) versions:
- Qlik Sense Enterprise on Windows May 2024 patch 24
- Qlik Sense Enterprise on Windows November 2024 patch 18
- Qlik Sense Enterprise on Windows May 2025 patch 6
- Qlik Sense Enterprise on Windows November 2025 IR, and all subsequent versions, such as May 2026 IR and upward
In some instances, the Qlik Sense patch installer updates service binaries but does not remove leftover node_modules folders from previous installations. The old request/node_modules/tough-cookie directories may still exist on disk even though the running service no longer uses them.
If you notice stale folders post-upgrade:
- Run the following PowerShell script as Administrator to clean up stale folders:
# Qlik Sense - tough-cookie stale folder cleanup # Run as Administrator after upgrading to v14.231.26 or later # Take a backup or snapshot before running Write-Host "Starting tough-cookie cleanup..." -ForegroundColor Cyan # Step 1 - Stop Service Dispatcher (this will stop all dependent Qlik Sense services) Stop-Service -Name "QlikSenseServiceDispatcher" -Force -ErrorAction SilentlyContinue Write-Host "Stopped: QlikSenseServiceDispatcher" -ForegroundColor Yellow Start-Sleep -Seconds 5 # Step 2 - Remove tough-cookie directories $paths = @( "C:\Program Files\Qlik\Sense\ConverterService\node_modules\tough-cookie", "C:\Program Files\Qlik\Sense\DownloadPrepService\node_modules\request\node_modules\tough cookie", "C:\Program Files\Qlik\Sense\MobilityRegistrarService\node_modules\request\node_modules\tough cookie", "C:\Program Files\Qlik\Sense\NotifierService\node_modules\request\node_modules\tough-cookie" ) foreach ($path in $paths) { if (Test-Path $path) { Remove-Item -Path $path -Recurse -Force Write-Host "Removed: $path" -ForegroundColor Green } else { Write-Host "Not found (already clean): $path" -ForegroundColor Gray } } Write-Host "`nCleanup complete. Restart Service Dispatcher manually to bring all services back online." -ForegroundColor CyanThis script may need to be re-run after any future Qlik Sense Enterprise on Windows patch or reinstallation, as the installer may restore these directories.
The script is provided as is and to be used at your own risk.
- Restart the Qlik Sense Service Dispatcher service
Internal Investigation ID(s)
- SUPPORT-2237
-
Qlik NPrinting and the CVE-2025-32433 Erlang/OTP vulnerability
Erlang/Open Telecom Platform (OTP) has disclosed a critical security vulnerability: CVE-2025-32433. Is Qlik NPrinting affected by CVE-2025-32433? Reso... Show MoreErlang/Open Telecom Platform (OTP) has disclosed a critical security vulnerability: CVE-2025-32433.
Is Qlik NPrinting affected by CVE-2025-32433?
Resolution
Qlik NPrinting installs Erlang OTP as part of the RabbitMQ installation, which is essential to the correct functioning of the Qlik NPrinting services.
RabbitMQ does not use SSH, meaning the workaround documented in Unauthenticated Remote Code Execution in Erlang/OTP SSH is already applied. Consequently, Qlik NPrinting remains unaffected by CVE-2025-32433.
All future Qlik NPrinting versions from the 20th of May 2025 and onwards will include patched versions of OTP and fully address this vulnerability.
Environment
- Qlik NPrinting
-
Security fix for Qlik Talend Administration Center cross-site scripting vulnerab...
Executive Summary A stored cross-site scripting security issue in the Qlik Talend Administration Center has been identified. This issue was resolved ... Show MoreExecutive Summary
A stored cross-site scripting security issue in the Qlik Talend Administration Center has been identified. This issue was resolved in a patch, which is already available.
This issue was discovered by Ahsan.
Affected Software
All versions of Qlik Talend Administration Center before Patch_20260123_QTAC-1883 (cumulative patch)_R2026-01_v1-8.0.1 are affected.
Severity Rating
Using the CVSS V3.1 scoring system (https://nvd.nist.gov/vuln-metrics/cvss), this issue is rated medium.
Vulnerability Details
CVE-2026-9056 (cve.org)
Severity: CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:C/C:L/I:L/A:N: (5.4 Medium)
A stored cross-site scripting vulnerability has been found in Qlik Talend Administration Center. An attacker with permission to manage servers can store an XSS payload that can be triggered by a different user.
Resolution
Upgrade at the earliest. The following table lists the patch versions addressing the vulnerability (CVE-2026-9056).
Always update to the latest version. Before you upgrade, check if a more recent release is available.
Product Patch Release Date Qlik Talend Administration Center QTAC-1883 January 23, 2026 -
Security fix for Qlik Talend Administration Center URL access control vulnerabil...
Executive Summary A broken access control issue has been identified in Qlik Talend Administration Center, which allows a user with View permission to... Show MoreExecutive Summary
A broken access control issue has been identified in Qlik Talend Administration Center, which allows a user with View permission to modify the Qlik Talend Studio update URL. This issue was resolved in a patch, which is already available.
This issue was discovered by Kaushik Roy.
Affected Software
All versions of Qlik Talend Administration Center before Patch_20251121_QTAC-1471_R2025-11_v1-8.0.1.
Severity Rating
Using the CVSS V3.1 scoring system (https://nvd.nist.gov/vuln-metrics/cvss), this issue is rated high.
Vulnerability Details
CVE-2026-9057: cve.org
Severity: CVSS:3.1/AV:N/AC:H/PR:L/UI:N/S:C/C:H/I:H/A:N: (8.2 High)
A broken access control issue has been identified in the Qlik Talend Administration Center, which allows a user with View permission to modify the Qlik Talend Studio update URL. This could be exploited to download malicious software to a Qlik Talend Studio instance.
Resolution
Upgrade at the earliest. The following table lists the patch versions addressing the vulnerability (CVE-2026-9057).
Always update to the latest version. Before you upgrade, check if a more recent release is available.
Product Patch Release Date Qlik Talend Administration Center QTAC-1471 November 21, 2025 -
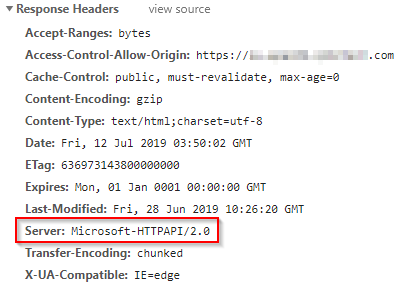
Qlik Analytics: Server Information In HTTP Header - Microsoft-HTTPAPI/2.0
HTTP Response Header exposes Microsoft-HTTPAPI/2.0 as the server source. An attacker could use this information to expose known vulnerabilities for th... Show MoreHTTP Response Header exposes Microsoft-HTTPAPI/2.0 as the server source. An attacker could use this information to expose known vulnerabilities for the server source.
Resolution
This header is included in the HTTP header by .NET framework, which means it can not be directly controlled by Qlik software.
The header is only added in Qlik software that runs in Windows environment, for example Qlik Sense Enterprise for Windows and QlikView Web Server.
There are two main approaches to removing this HTTP header;- Disable the server header for WCF Services in the Windows registry, as described in https://blogs.msdn.microsoft.com/dsnotes/2017/12/18/wswcf-remove-server-header/
- Suppress the HTTP header through a reverse proxy if this exists in front of Qlik Sense in the current deployment. For option details on this option, consult reverse proxy documentation. If you require assistance implementing the solution, our professional services are happy to be engaged.
Environment
Qlik Sense Enterprise on Windows, all version
QlikView, all versions
Qlik NPrinting, all versionsInternal Investigation IDs:
- QLIK-90522
-
Qlik Cloud: Content restricted or unavailable with Embedded Analytics User role ...
The Embedded Analytics User role is a role available in Qlik Cloud for use cases where your users should not access the Qlik Cloud hub directly. If t... Show More -
Qlik Sense Enterprise on Windows and the PostgreSQL CVE-2025-1094 vulnerability
PostgreSQL has identified a vulnerability (CVE-2025-1094) that allows for SQL injection under certain scenarios. For more information, see CVE-2025-10... Show MorePostgreSQL has identified a vulnerability (CVE-2025-1094) that allows for SQL injection under certain scenarios. For more information, see CVE-2025-1094: PostgreSQL quoting APIs miss neutralizing quoting syntax in text that fails encoding validation.
Resolution
To allow for quick mitigation of PostgreSQL vulnerabilities, Qlik offers the ability to run and manage your own PostgreSQL instance independently of what Qlik Sense Enterprise on Windows is shipped with. This allows for direct control of your PostgreSQL instance and facilitates maintenance without a dependency on Qlik Sense. Further Database upgrades can then be performed independently and in accordance with your corporate security policy when needed, as long as you remain within the supported PostgreSQL versions.
Recommendations
Upgrade to Qlik Sense Enterprise on Windows May 2025 IR
Qlik Sense Enterprise on Windows May 2025 IR includes PostgreSQL 14.17 in its installer. See the System Requirements for details.
Upgrade PostgreSQL
If you have already installed a standalone PostgreSQL database, or if you have used the Qlik PostgreSQL Installer (QPI) to upgrade and decouple your previously bundled database, then you can upgrade PostgreSQL at any time. This means you control maintenance and can immediately react to potential PostgreSQL security concerns by upgrading to a later service release or a later major version.
See Qlik Sense Enterprise on Windows: How To Upgrade Standalone PostgreSQL.
Verify your Qlik Sense Enterprise on Windows version's System Requirements before committing to a PostgreSQL version.
Unbundle and upgrade PostgreSQL using QPI
If you have not yet installed a standalone PostgreSQL instance, this is the preferred method to gain direct control to upgrade at your own pace. For instructions, see Upgrading and unbundling the Qlik Sense Repository Database using the Qlik PostgreSQL Installer.
Manually switch to a dedicated PostgreSQL database
An alternative method to migrate to a standalone PostgreSQL instance is available in How to configure Qlik Sense to use a dedicated PostgreSQL database.
Related Content
- System requirements for Qlik Sense Enterprise
- Qlik Sense Enterprise on Windows: How To Upgrade Standalone PostgreSQL
- Upgrading and unbundling the Qlik Sense Repository Database using the Qlik PostgreSQL Installer
- How to configure Qlik Sense to use a dedicated PostgreSQL database
Internal Investigation ID(s)
SUPPORT-896
Environment
- Qlik Sense Enterprise on Windows
-
Critical Security fix for the Qlik Talend JobServer and Talend Runtime (CVE-2026...
Executive Summary A critical security issue in the Talend JobServer and Talend Runtime has been identified. This issue was resolved in later patches, ... Show MoreExecutive Summary
A critical security issue in the Talend JobServer and Talend Runtime has been identified. This issue was resolved in later patches, which are already available. If the vulnerability is successfully exploited, an attacker could gain full remote code execution on the Talend JobServer and Talend Runtime servers.
This issue was discovered by Harpreet Singh (@TheCyb3rAlphaProfession), Security Researcher.
Affected Software
- All versions of Talend JobServer before TPS-6017 (8.0) or TPS-6018 (7.3).
- All versions of Talend Runtime before 8.0.1.R2026-01-RT or 7.3.1-R2026-01
Severity Rating
Using the CVSS V3.1 scoring system (https://nvd.nist.gov/vuln-metrics/cvss), this issue is rated CRITICAL.
Vulnerability Details
CVE-2026-6264
Severity: CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H (9.8 Critical)
A critical vulnerability has been found in the Talend JobServer and Talend Runtime that allows unauthenticated remote code execution
The attack vector for this vulnerability is the JMX monitoring port of the Talend JobServer. The vulnerability can be mitigated for the Talend Jobserver by requiring TLS client authentication for the monitoring port. However, the patch will need to be applied to fully mitigate the vulnerability.
For Talend Runtime, the vulnerability can be mitigated by disabling the JobServer JMX monitoring port, which is disabled by default from the 8.0 R2024-07-RT patch.Resolution
Recommendation
Upgrade at the earliest. The following table lists the patch versions addressing the vulnerability (CVE-2026-6264).
Always update to the latest version. Before you upgrade, check if a more recent release is available.
Product Patch Release Date Talend JobServer 8.0 TPS-6017 January 16, 2026 Talend Jobserver 7.3 TPS-6018 January 16, 2026 Talend Runtime 8.0 8.0.1.R2026-01-RT January 24, 2026 Talend Runtime 7.3 7.3.1-R2026-01 January 24, 2026 -
Qlik Sense Enterprise on Windows: Securing and Hardening Server
Security of Qlik Sense Enterprise on Windows can be approached in the below discrete areas. All these areas provide different options for increasing s... Show MoreSecurity of Qlik Sense Enterprise on Windows can be approached in the below discrete areas. All these areas provide different options for increasing security in a deployment, and thereby mitigating vulnerabilities and protecting against attackers.
Content:
- 1. Authentication
- 2. Authorization
- Security Rules
- Section Access
- 3. Operating System Hardening
- Step 1: Disabling protocols and ciphers
- Step 2: Firewalls
- Step 3: Service Account Permission
- Step 4: Anti-Virus
- Step 5 (Optional): FIPS
- 4. PostgreSQL Hardening
- 5. Generalized Web Server best practices
- Apply a trusted certificate
- Optional: Additional HTTP Response Headers
Be aware that a high level of server hardening can lead to failure in your deployment. Be mindful of always having a backup to restore to in case your configuration leads to irreversible failure.
1. Authentication
Qlik Sense Enterprise on Windows supports multiple different Authentication Solutions;
- Windows (NTLM)
- Kerberos
- Ticketing
- SAML
- JWT
- Header
- Anonymous
Qlik can not specify which authentication method is appropriate for each deployment. It is advisable to review currently supported alternatives within your organization and/or Identity Provider (IdP) to implement the most suitable solution for your use case.
2. Authorization
Qlik Sense Enterprise on Windows provides two levels of native authorization in the product.
Security Rules
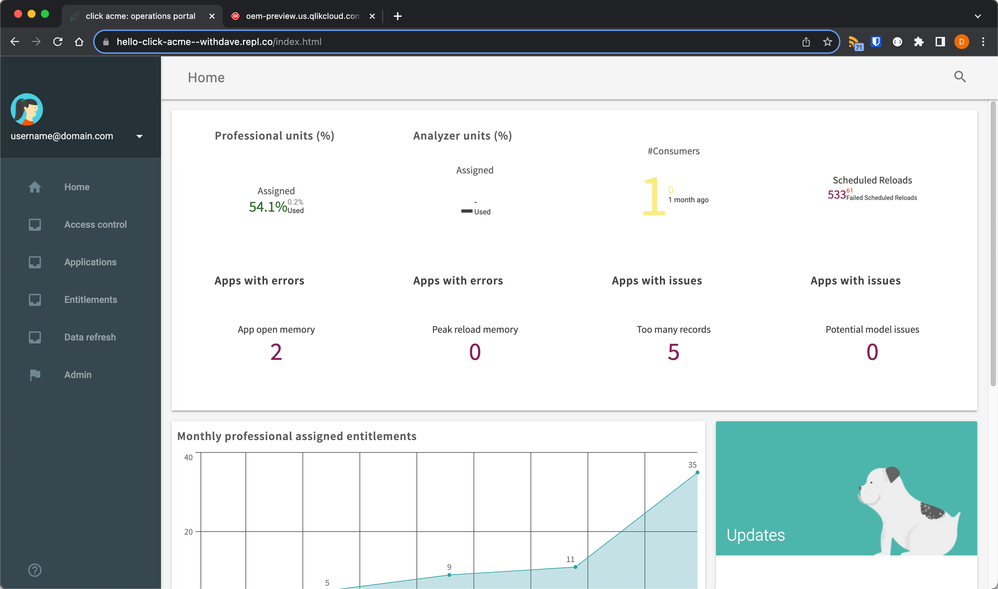
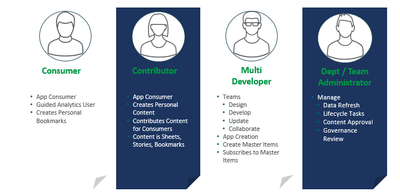
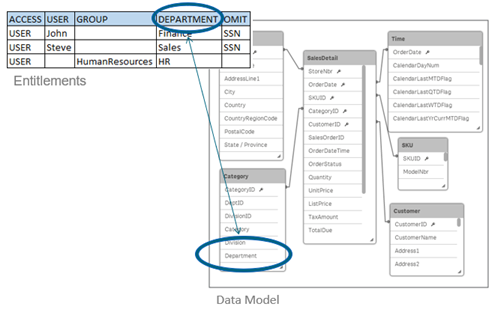
Attribute based access control (ABAC), which is configured through Qlik Sense security rules. This article will not go in depth on how to best implement security rules for your requirements, but it is highly recommended to think of your users based on the capabilities that you intend to provide them. For example different roles and capabilities as shown in image below, allows for a security rule framework to be designed and implemented. This can be done either by yourself by referencing Qlik Sense Help for Administrators and available assets or by engaging with a Qlik Consultant or Qlik Partner.
Section Access
Row level data reduction, which is configured through Section Access at Qlik Sense app level. This article will not go in depth on Section Access implementation, but with this reduction a single file can be used to hold the data for a number of users or user groups. Qlik Sense uses the information in the section access for authentication and authorization, and dynamically reduces the data, so that users only see their own data.
3. Operating System Hardening
Qlik Sense Enterprise on Windows inherits the available protocols, cipher suites, key exchanges and other security hardening which are enabled on the Windows Server operating Qlik Sense.
Step 1: Disabling protocols and ciphers
Windows Server has a lot of protocols enabled by default; however protocols, ciphers, hashes and key exchanges that are considered deprecated or not secure enough should be disabled. There are many ways of doing this, and the Windows administrator and security experts should be consulted so that local policies are accurately applied. For simplicity, understanding and a good overview IIS Crypto 3.0 can be a good tool for evaluating current Windows configuration and applying changes.
Keep in mind that "Best Practice" today might not be recommended in the near future, what was considered "safe" a while ago is not necessarily considered so today. For this reason, it is also important to regularly scan servers for potential vulnerabilities and revisit configurations as required.The Windows Server needs to be restarted for these settings changes to take effect. It is also important to ensure that all components running on the server still operate as expected after hardening is applied, for example, older non-Qlik software might not be compliant with the latest options and standards.
Step 2: Firewalls
Firewalls typically should be closed, with required ports only opened for intended purposes.
See Qlik Sense Enterprise on Windows ports overview for details on required port based on the deployed architecture.Step 3: Service Account Permission
For most organizations, local administrator rights allow for an easier deployment, but Qlik Sense Enterprise on Windows does not require local administrator rights in order to function. This can be an attractive option inside some organizations. This will require additional configuration of boot strap mode as described in Qlik Sense Enterprise on Windows Services.
For a brief overview of the rights needed by a Qlik Sense Enterprise service account:- Full control over the share used by Qlik Sense Enterprise
- Full control over the installation directory (default: C:\Program Files\Qlik)
- Full control over %ProgramData%\Qlik
- Full control over any folders used as data connections
Qlik Sense Enterprise for Windows does not officially support Group Managed Service Accounts (gMSA), but it can operate using one. The initial barrier is that the installer requires a service account and password to be entered during installation. A domain or local account could be substituted for the install stages only to be swapped out in the Windows Services applet (services.msc) after installation. Some functionality may require workarounds (e.g. A User Directory Connection to Active Directory).
Step 4: Anti-Virus
Qlik Sense Enterprise on Windows does require exceptions from anti-virus scan to avoid potential disk I/O conflicts. Refer to Qlik Sense Folder And Files To Exclude From AntiVirus Scanning for more details.
Step 5 (Optional): FIPS
Qlik Sense Enterprise on Windows can run with Federal Information Processing Standards (FIPS) enabled on the Windows Server. This does require a few adjustments of configuration files due to Qlik using non-FIPS compliant algorithms for minor tasks like hash checks. See Running Qlik Sense on Windows systems with FIPS compliance enabled for more details on Qlik Sense and FIPS.
4. PostgreSQL Hardening
Qlik Sense Enterprise on Windows uses PostgreSQL to store meta-data relating to a Qlik Sense site. In multi-node sites or sites where PostgreSQL is isolated from Qlik Sense Enterprise for Windows additional security can be applied;
- Database Traffic Encryption
- Hardening what endpoints are allowed to connect to PostgreSQL as described in PostgreSQL: postgresql.conf and pg_hba.conf explained
5. Generalized Web Server best practices
Qlik Sense Proxy service bundled with Qlik Sense Enterprise on Windows is simply a web-service. This means applying general practice guidance but in the context of Qlik Sense as described below.
Apply a trusted certificate
Qlik Sense Enterprise on Windows acts as a Certificate Authority (CA) during initial installation and signs a certificate that is applied on all encrypted traffic between Qlik Sense services. The same Qlik Sense signed certificate is applied as default certificate also for incoming connections from users accessing Qlik Sense Hub and QMC. This default certificate is not intended for production use, unless user access to Qlik Sense comes through a network load balancer or reverse proxy that trusts the Qlik Sense certificate. For direct user access to Qlik Sense Proxy, a fully trusted certificate can typically be acquired from your local IT and then applied on the Qlik Sense Proxy service.
As of July 2019, Qlik Sense Enterprise on Windows support SHA1 and SHA2 certificates. If SHA384 or SHA512 certificates are needed, then a network load balancer or reverse proxy can be configured in front of Qlik Sense which offloads to Qlik Sense.
Optional: Additional HTTP Response Headers
There are numerous HTTP response headers that can be used in attempting to secure a server. Below are a couple of the most common ones, but as always it is recommended to consult local IT and web security expert on what the recommendations are.
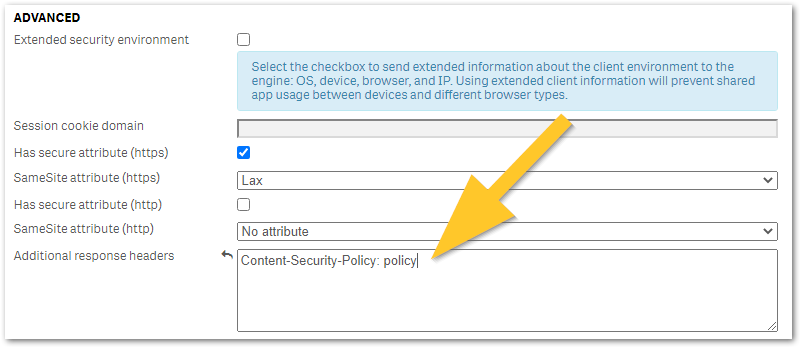
Any additional HTTP response header values can be configured in Qlik Sense Virtual Proxy settings under Additional response headers as shown in the below image and described in Qlik Sense for Administrators: Virtual Proxies. It is recommended to trial any header changes in a new virtual proxy, as poor configuration may accidentally lock you out from Qlik Sense access.
- HTTP Strict Transport Security (HSTS) HTTP Strict Transport Security (HSTS) is an opt-in security enhancement which any web application can support through the use of a special response header. When a supported browser receives this header that browser will prevent any communication sent over HTTP in the future and will redirect all traffic over HTTPS instead. Caution is advised when implementing HSTS, as it might block HTTP access to certain pages that actually requires it or needs to be excluded from HSTS. See MDN Web Docs: Strict-Transport-Security for more details on configuration options.
- Optional: X-Content-Type-Options X-Content-Type-Options response HTTP header is a marker used by the server to indicate that the MIME types advertised in the Content-Type headers should not be changed and be followed. This allows to opt-out of MIME type sniffing.
- X-Frame-Options will prevent the site to be embedded in an iFrame, which can effective mitigate against ClickJacking attacks
- Content-Security-Policy: policy (old: X-XSS-Protection) improves security against some types of XSS (cross-site scripting) attacks.
Policy is a placeholder for your policy of choice and cannot be used as a value. See Writing a Policy (Mozilla) for examples.
-
Qlik’s Response to Apache Tika vulnerability CVE-2025-66516
Executive Summary In December 2025, the Apache Project announced a vulnerability in Apache Tika (CVE-2025-66516) and provided patches to resolve the ... Show MoreExecutive Summary
In December 2025, the Apache Project announced a vulnerability in Apache Tika (CVE-2025-66516) and provided patches to resolve the issue. Qlik has been reviewing our usage of the Apache Tika product suite and has identified a limited impact as follows.
Affected Software
Apache Tika is used in several Qlik products. However, the vulnerability is only relevant to the case of a Talend Studio route that uses Apache Tika to parse PDFs.
No other use case or product is impacted by the vulnerability. Qlik Cloud and Talend Cloud are not impacted by this vulnerability.
Nevertheless, we are patching all our products that contain Apache Tika out of an abundance of caution. Be on the lookout for a series of product patches for supported and affected versions.
Resolution
Recommendation
The releases listed in the table below contain the updated version of Apache Tika, which addresses CVE-2025-66516.
Always update to the latest version. Before you upgrade, check if a more recent release is available.
Product Patch Release Date Talend Studio R2025-11v2 December 16, 2025 Talend Administration Center QTAC-1472 December 19, 2025 Talend ESB Runtime R2025-12-RT December 19, 2025 Talend Remote Engine Gen 2. Connectors 1.58.8 December 23, 2025 Talend Data Stewardship TPS-6013 December 23, 2025 Talend Data Preparation TPS-6016 January 16, 2026 -
Qlik Talend Studio: It is very slow to open a Job
Talend Studio opens very quickly, but when attempting to open a Job, the process becomes very slow, and the following error messages are displayed in ... Show MoreTalend Studio opens very quickly, but when attempting to open a Job, the process becomes very slow, and the following error messages are displayed in the .log file:
: !STACK 0 java.lang.IllegalStateException: java.util.concurrent.TimeoutException: Timeout when waiting for component server initialization: -Dtalend.studio.sdk.startup.timeout=2
Resolution
Prevent the infosec software from redirecting the port to bind.
Cause
The operation manager enabled feature from the cybersecurity software that allows to redirect the request.
Environment
-
Qlik Stitch: Snowflake Stitch and the PUBLIC role
Stitch Support frequently receives questions regarding the invocation of the PUBLIC role with Snowflake. When setting up a database user following Cre... Show MoreStitch Support frequently receives questions regarding the invocation of the PUBLIC role with Snowflake. When setting up a database user following Create a Stitch database and database user (Qlik Stitch Documentation), users will notice that the Stitch user executes GRANT statements on the PUBLIC role. This behavior can raise questions about role-based access and security implications within Snowflake.
Resolution
Manually adjust permissions in Snowflake as needed. If you prefer Stitch offers a more streamlined approach in its behavior, please submit a feature request. Refer to New Process for Submitting a Feature Request for All Talend Customers and Partners on how to submit a feature request.
Cause
By default, Stitch grants the PUBLIC role access to schemas and objects it creates in Snowflake. This behavior often raises questions from users who are concerned about broad access permissions.
The reason Stitch does this is because it cannot assume which specific roles or users in your organization should have access to the data. Granting access to the PUBLIC role ensures that Stitch can write data successfully without making assumptions about your internal role structure.
This default behavior is not a requirement from Snowflake itself, but rather a design decision by Stitch to simplify initial setup and avoid permission-related sync failures.
If this approach does not align with your organization’s security policies, you may manually revoke access from the PUBLIC role after the initial sync. However, this step must be repeated each time a new integration runs or a new schema is created, which may not be scalable.
Snowflake supports granular permission control via the REVOKE command, allowing you to adjust access as needed:
🔗 REVOKE <privileges> … FROM ROLE | docs.snowflake.com
While this manual revocation process works, it requires ongoing attention. If tighter access control is a priority and manual intervention isn’t feasible, you may want to consider alternative destinations or workflows.
Environment
-
Qlik Sense and Vulnerability “CVE-2025-7783” in NPM Library form-data
Qlik Sense and Vulnerability “CVE-2025-7783” in NPM Library form-data In mid-July 2025, a vulnerability was disclosed in the NPM library form-data (Gi... Show MoreQlik Sense and Vulnerability “CVE-2025-7783” in NPM Library form-data
In mid-July 2025, a vulnerability was disclosed in the NPM library form-data (GitHub Security Advisory). Qlik became aware of this issue through its standard Secure Development Lifecycle (SDL) processes.
Following an internal review, Qlik R&D and Security teams identified that potentially vulnerable versions of the form-data library were included in some installations of Qlik Sense Enterprise for Windows. However, due to the specific way Qlik utilizes this library, the conditions required for exploitation are not met.
Although the vulnerability was determined to be non-exploitable within Qlik Sense, customers who prefer to upgrade to a version that includes the patched form-data library can do so by installing one of the following releases:
- May 2025 Patch 6
- November 2024 Patch 18
- May 2024 Patch 24
Note: An earlier version of this information was mistakenly published indicating that this CVE was directly related to Qlik Sense for Windows.
-
Qlik Sense Enterprise on Windows: Compatibility information for third-party SSL ...
A third-party certificate was configured in the Qlik Sense Proxy, but is not being used. The connection is not private" NET::ERR_CERT_COMMON_NAME_INVA... Show MoreA third-party certificate was configured in the Qlik Sense Proxy, but is not being used.
The connection is not private" NET::ERR_CERT_COMMON_NAME_INVALID may be displayed on HUB access.
Qlik Sense Enterprise on Windows uses self-signed and self-generated certificates to protect communication between services, as well as user web traffic to the hub and management console. It is possible to use a third-party-issued SSL certificate to protect client web traffic. Using the self-signed certificate will cause a certificate warning to be displayed in the web browser (such as Google Chrome or Internet Explorer).
If the third-party certificate for the Qlik Sense Proxy Service is not fully compatible with Qlik Sense or it does not have the correct attributes and cyphers, the Qlik Sense Repository Service will revert to using the default certificates. The following error may occur in the Proxy Security logs:
Example: C:\ProgramData\Qlik\Sense\Log\Proxy\Trace\HOSTNAME_Security_Proxy.txtNo private key found for certificate 'CN=qliksense.domain.com' ([CERTIFICATE THUMBPRINT HERE]) Couldn't find a valid ssl certificate with thumbprint [CERTIFICATE THUMBPRINT HERE] Reverting to default Qlik Sense SSLCertificate Set certificate 'CN=qliksenseserver1.domain.com' ([CERTIFICATE THUMBPRINT HERE]) as SSL certificate presented to browser
Resolution:
In order for Qlik Sense Enterprise to correctly recognize the third-party certificate as valid, the certificate will have to meet the following requirements:
Note: Root and Intermediate CA certificates need to be correctly installed. Should any be missing, Qlik Sense proxy will not use the server certificate and will revert back to using the self-signed certificate instead.
Certificates that are known to work well with Qlik Sense have the following attributes:- Certificates that are x509 version 3. More information including filename extensions under https://en.wikipedia.org/wiki/X.509
- Use signature algorithm sha256RSA
- Use signature hash algorithm sha256
- Signed by a valid, and OS/browser configured , CA
- Are valid according to date restrictions (valid from/valid to)
- Key in format CryptoAPI (not in CNG)
- The certificate itself has to contain private key no matter what Qlik Sense version.
Related Content:
How to: Change the certificate used by the Qlik Sense Proxy to a custom third party certificate
-
Restricting Access to Qlik Cloud Talend Platform
While Qlik Cloud provides robust data connectivity options through the Data Movement Gateway, some organizations require additional controls to restri... Show MoreWhile Qlik Cloud provides robust data connectivity options through the Data Movement Gateway, some organizations require additional controls to restrict access to the Qlik Cloud Talend platform itself, not only to data connections.
While Qlik Cloud does not currently support full tenant-level access restriction via PrivateLink, it does offer:
- IP-based access control via Web Integrations
- Strong authentication and security policies
- Gateway-based PrivateLink support for data connectivity
- Cryptographically secure gateway communication
This article outlines these available options and limitations for securing tenant access at the platform level.
Content
- Does Qlik Cloud support IP Allowlist for tenant access?
- Are there network-level restrictions available for accessing the Qlik Cloud tenant?
- What are the available options for securing tenant access beyond standard authentication?
- Understanding Gateway Security Architecture
- Future Plans
Does Qlik Cloud support IP Allowlist for tenant access?
Yes. Qlik Cloud supports IP allowlisting through Web Integrations, which can be configured to restrict access to the tenant based on specific IP addresses.
See Managing web integrations for details.
Are there network-level restrictions available for accessing the Qlik Cloud tenant?
Qlik Talend Data Integration supports private connections for tenant-level access. Does Qlik Cloud support a similar, solution, such as Azure or AWS PrivateLink?
No, Qlik Cloud does not support Azure PrivateLink for tenant-level access in the same way Talend Cloud does.
- In Qlik Talend Data Integration, PrivateLink can be used to restrict access to the entire tenant.
- In Qlik Cloud, PrivateLink is supported only for data connectivity via a customer-managed gateway.
- The gateway acts as the endpoint for PrivateLink, but it does not restrict access to the Qlik Cloud web interface.
- See Support private connections in Qlik Talend Data Integration for details.
What are the available options for securing tenant access beyond standard authentication?
Qlik Cloud offers several security features for tenant access:
- Multi-Factor Authentication (MFA)
- OAuth
- Content Security Policy (CSP)
- API Keys
- Web Integrations (IP Allowlist)
See Securing the system.
Understanding Gateway Security Architecture
When using the Data Movement Gateway, Qlik Cloud ensures secure communication through a multi-step cryptographic process:
- Key Generation & Registration:
Upon installation, the gateway generates a private/public key pair and a key ID (kid). The public key and key ID are registered in Qlik Cloud by the tenant admin. - Secure WebSocket Establishment:
- The gateway initiates a TLS-secured WebSocket (WSS) connection to Qlik Cloud.
- During this handshake:
- The gateway verifies QCS’s certificate.
- Qlik Cloud verifies the JWT sent by the gateway, ensuring it includes the correct key ID and is signed with the gateway’s private key.
- This confirms a cryptographic match to the registered public key and key ID.
- Channel Key Derivation:
- Both sides generate ECDH key pairs and exchange secrets.
- A channel key is derived and used to encrypt all traffic over the WebSocket.
- This key is re-derived upon reconnection or restart, ensuring session-level encryption.
This architecture ensures that all data movement operations are secure, authenticated, and encrypted end-to-end.
Future Plans
If full tenant isolation via PrivateLink is a critical requirement, please submit a feature request via Qlik Ideation.
Environment
- Qlik Cloud
- Qlik Talend Data Integration
-
Qlik Sense Enterprise on Windows and Node.js
Node.js comes bundled with Qlik Sense Enterprise on Windows. Its version depends on the Qlik Sense released currently installed. How do I know which v... Show MoreNode.js comes bundled with Qlik Sense Enterprise on Windows. Its version depends on the Qlik Sense released currently installed.
How do I know which version of node.js is used by Qlik Sense?
You can verify the version of any of the third-party integrations Qlik Sense makes use of by:
- Using the Qlik Sense API and calling About Service API: thirdParty: Get, which returns details including information about copyright, version, licensing, and legal notices.
- Accessing the below URL in a browser, where qlikserver.domain.local is replaced with your Qlik Sense server hostname:
https://qlikserver.domain.local/api/about/v1/thirdParty
How do I upgrade my version of node.js is used by Qlik Sense?
You may want to upgrade node.js, specifically in response to a security vulnerability. To do so, upgrade Qlik Sense Enterprise on Windows. When upgrading Qlik Sense, the currently installed node.exe will be replaced with the version Qlik Sense comes bundled with at this release.
Can I install or upgrade a separately installed instance of node.js?
Installing Qlik Sense installs node.exe side-by-side in the following location: C:\Program Files\Qlik\Sense\ServiceDispatcher\Node.
If you install node.js manually it will typically be installed in C:\Program Files\nodejs and the Windows environment variable will point to this location by default (i.e. running node -v to get the version will result in providing the version of node found in C:\Program Files\nodejs).
As Qlik Sense will not register any Windows environment variable for node.js, it will not tamper with any settings affecting already installed node.js instances. Therefore it is safe to upgrade your separate instance of Node.js.
Environment
- Qlik Sense Enterprise all versions
Related Content
Third-party and middleware software integrated with Qlik Sense Enterprise on Windows
-
Qlik Talend Administration Center 8.0 and CVE-2025-24813
A deployed 8.0.1 Talend Administration Center instance is bundled with Apache Tomcat 9.0.91. This Tomcat version has been flagged as being impacted by... Show MoreA deployed 8.0.1 Talend Administration Center instance is bundled with Apache Tomcat 9.0.91. This Tomcat version has been flagged as being impacted by CVE-2025-24813.
Resolution
At this time, CVE-2025-24813 does not apply to the Talend Administration Center (TAC) webapp. The reason Talend Administration Center is not impacted at this time, is because Tomcat installed with Talend Administration Center has disabled the "Writes enabled for the default servlet" option (disabled by default); A prerequisite for being suspectable to an attack would be to have that setting enabled.
While the Talend Administration Center webapp itself is not impacted by the CVE, if users desire to remove those vulnerable jars removed from security scans (whether due to preference, security audit, or other considerations), users have the following options to pursue:
- If the current Tomcat instance that hosts Talend Administration Center 8.0 is version 9.0.x, users can upgrade Tomcat to 9.0.100 or higher.
- If the current Tomcat is using 10.1.34 or a prior version, users can upgrade Tomcat to at least 10.1.40 (or higher) and patch the TAC instance to QTAC-969.
Please note if users plan to upgrade Talend Administration Center from TPS-5552 or earlier (Using Tomcat 9) to QTAC-969 or higher for TAC 8.0, the recommended path would be to deploy both Apache Tomcat 10.1.40 (or higher) and Java 17 to address this release. (One recommended option is to completely reinstall Tomcat & Talend Administration Center with the new installer and point to the new DB).
If users manually deploy Tomcat 10.1.40 (or a later version) alongside the Talend Administration Center to an instance, and wish to verify that the aforementioned flag(s) are disabled, kindly inspect the "web.xml" file located in (<Root Folder>/apache-tomcat/conf). Proceed to approximately lines 124-135, and examine the following configuration for the "org.apache.catalina.servlets.DefaultServlet":
<servlet> <servlet-name>default</servlet-name> <servlet-class> org.apache.catalina.servlets.DefaultServlet </servlet-class> <init-param> <param-name>readonly</param-name> <param-value>false</param-value> </init-param> <load-on-startup>1<load-on-startup> </servlet>The example shown above illustrates that the value is set to "false", signifying that it is write-enabled. If users want that functionality disabled, change the "param-value" flag to false, save the changes, and subsequently restart Tomcat (either via the start/stop bat/sh script, or with the service).
Internal Investigation ID(s)
QTAC-918
Environment
-
Qlik Data Integration products: PGAdmin Next.js Middleware Authorization Bypass ...
Is Qlik Replicate affected by CVE-2025-29927? (Next.js Middleware Authorization Bypass Vulnerability (CVE-2025-29927) – Qualys ThreatPROTECT) Resoluti... Show MoreIs Qlik Replicate affected by CVE-2025-29927? (Next.js Middleware Authorization Bypass Vulnerability (CVE-2025-29927) – Qualys ThreatPROTECT)
Resolution
None of Qlik's Data Integration products (Qlik Replicate, Qlik Compose, Qlik Enterprise Manager, Qlik Catalog) use next.js and are not exposed to CVE-2025-29927.
Review if other programs are installed that are affected and uninstall or upgrade them as required, such as PGAdmin.
Note that while Qlik Replicate uses the PostgreSQL driver when PostgreSQL is used as a source or target endpoint, PGAdmin does not need to be installed on the server.
Environment
- Qlik Replicate
-
Qlik Sense Management Console fails to open when Virtual Proxy set to Always Ano...
A virtual proxy which was configured to use Always Anonymous is not intended to be used for administration. While Qlik Sense will prompt for login whe... Show MoreA virtual proxy which was configured to use Always Anonymous is not intended to be used for administration. While Qlik Sense will prompt for login when accessing the Qlik Sense Management Console (QMC), the Management Console cannot be navigated successfully.
Beginning with November 2023, access will fail with:
An error occurred
The operation failed due to insufficient privilegesAs well as:
400
Bad RequestPrevious version of Qlik Sense may succeed with the login but not allow navigation.
Resolution
Do not use a Virtual Proxy configured to use Always Anonymous as authentication method. Always have a Virtual Proxy ready which requires authentication. For information on how to create a new Virtual Proxy, see Qlik Sense: How to create a new Virtual Proxy.
If you have locked yourself out of the Qlik Sense Management Console by modifying the only available Virtual Proxy, change the enabled authentication method directly in the Qlik Sense QSR database.
Manual steps to change the authentication method:
- Connect to the QSR using PGAdmin (see How to connect to the Qlik Sense Enterprise on Windows or Qlik NPrinting PostgreSQL database)
- Open the VirtualProxyConfig table
- In the row for your active Virtual Proxy, change the column AnonymousAccessMode value from 3 (Always Anonymous) to 0 (Requires Authentication)
- Save the changes
- Restart the database service
Cause
A secure Qlik Sense Enterprise Management Console when anonymous access is required.
Internal Investigation ID(s)
SHEND-1902
Environment
Qlik Sense November 2023 & Newer
-
Qlik Talend Administration Center: How to reset default credentials (security@co...
If unable to access TAC using default credential (security@company.com/admin), you have forgotten your password. You can reset it by following these s... Show MoreIf unable to access TAC using default credential (security@company.com/admin), you have forgotten your password.
You can reset it by following these steps:
- Establish a connection to the TAC database.
- In the TAC database, execute the following statement:
UPDATE 'user' set 'password'=0x21232F297A57A5A743894A0E4A801FC3 where id =<userID>;
Note that `0x21...` corresponds to the encrypted password for "admin". To identify the <userID> associated with the user whose password you wish to update, execute this query: select id, login from user; - Using the new password, log in to Talend Administration Center once again.
Related Content
Change the default password used to configure the TAC database
Environment